Recently our colleague Joshua Goode escalated to the Security Research team an investigation he was performing on several websites that presented the same indicators of compromise. There were small variations in what the final payload was, but the attack timeline was always the same.
Attack timeline
As Joshua initially pointed out and subsequently confirmed by me, the chain starts with the installation of the core-stab plugin, followed by other additional items. The following timeline depicts one of the many compromised sites we reviewed:
- Jan 10, 2023 @ 17:29:49.587 UTC – Core stab plugin upload – /wp-admin/update.php?action=upload-plugin
- Jan 10, 2023 @ 17:29:52.270 – /wp-content/plugins/core-stab/index.php
- Jan 11, 2023 @ 02:12:50.773 – /wp-admin/theme-install.php?tab=upload
- Jan 11, 2023 @ 02:12:57.862 – Classic theme upload – /wp-content/themes/classic/inc/index.php
- Jan 11, 2023 @ 03:37:58.870 – Another core-stab install
- Jan 11, 2023 @ 04:15:06.014 – Installation of a new plugin,
task-controller, /wp-content/plugins/task-controller/index.php - Jan 11, 2023 @ 08:23:26.519 – Installation of WP File Manager (Unsure if by attacker but this plugin is typical with a lot of malware)
The most common “coincidence” is that all users involved in this attack had their emails listed on at least one public password leak since 2019, which only corroborates the overall findings: the attacker(s) used compromised or leaked accounts to install the malware.
You can find more details on how the core-stab malware works, as well as detailed detection and blocking information for WP security experts, via WPScan.
What to do if my site was infected?
If you find the core-stab plugin installed on your site, the first thing you should do is remove it and then follow these next steps:
- Change all admin user’s passwords and make sure you’re using multi-factor authentication.
- Review all WordPress users and remove the ones you don’t recognize (especially the admin ones).
- Review for unused or unknown themes and plugins and remove anything unnecessary or unknown.
- Reinstall all your plugins since they may have been compromised.
- Review your theme for added or changed files that weren’t added or changed with your consent.
- Reinstall WordPress core files.
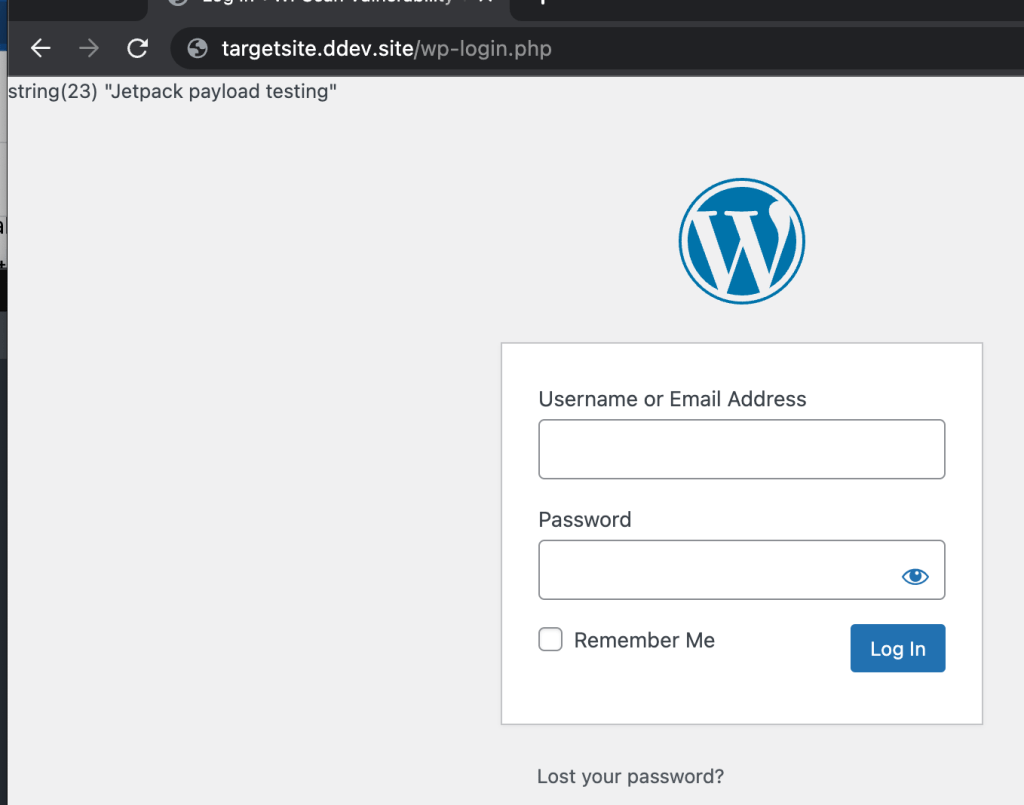
Finally, at Jetpack, we work hard to make sure your websites are protected from these types of vulnerabilities. We recommend that you have a security plan for your site that includes malicious file scanning and backups. The Jetpack Security bundle is one great WordPress security option to ensure your site and visitors are safe. This product includes real-time malware scanning, site backups, comment and form spam protection from Akismet, brute force attack protection, and more.
