It’s every website owner’s biggest fear: hearing that their site has been compromised. Though WordPress is a safe platform, all websites are vulnerable to attacks, especially if they haven’t taken the necessary measures to secure and protect their site from hackers.
But if your WordPress site is hacked and the damage is already done, hope is not lost. There are a few ways you can work to recover content, repair the harm, and most importantly, protect your website from future attacks.
On this page, we’ll answer the following questions:
- Emergency checklist to recover your hacked site
- How to know if your WordPress site has been hacked
- Why your site has been hacked
- The top five ways a WordPress site gets hacked.
- How to fix a hacked WordPress site
- How to prevent a WordPress site from being hacked
- FAQs about WordPress hacks
7-step emergency checklist to recover your hacked WordPress site
If your site is hacked, time is critical. Follow these steps immediately to regain control and begin the cleanup process.
- Isolate Your Site: Put your WP site into maintenance mode to prevent further damage and protect visitors.
- Contact Your Host: Inform your hosting provider. They can help identify server-level issues and provide logs.
- Scan for Malware: Use a tool like Jetpack Scan to find malicious files and code injections.
- Change All Passwords: Immediately reset passwords for WordPress admin, hosting, SFTP, and your database.
- Restore from a Clean Backup: If you have a recent, uninfected backup (like those from Jetpack Backup), restoring it is the fastest way to recover.
- Clean Infected Files: If a backup isn’t an option, manually remove malware or use a security plugin’s one-click fix feature.
- Harden Your Site: Once clean, take immediate steps to secure your site against future attacks.
How do I know if my WordPress site has been hacked?
(If you know your site has been hacked already, skip ahead and learn how to fix it.)
If your site is acting strangely and you’re not sure what’s wrong, it doesn’t necessarily mean that you’ve been hacked. You could be experiencing a software bug, hosting trouble, caching-related problem, or a number of other issues. It can sometimes be difficult to know, initially, whether your site has been hacked or if what you’re experiencing is due to other causes.
Signs that your site has been hacked:
1. Your website won’t load.
There are a lot of reasons why your website might not be loading. A malicious attack is just one of many possibilities. When you attempt to load your site, check the error message that displays. Some errors are generic enough that they aren’t particularly helpful in diagnosing the problem immediately, but knowing what kind of error you’re getting is the first step to diagnosing the cause.
Here are a few of the most common WordPress errors:
- HTTP 500 Internal Server Error. This is the most common error website visitors will encounter. For WordPress sites, you may see the error display as “Error Establishing a Database Connection,” “Internal Server Error,” or “Connection Timed Out.” In your server logs it will likely give the error code, “HTTP 500”. It’s a very generalized error and the only concrete thing it indicates is that there’s a problem on your site’s server. It could be due to a hacker, but it could also be a server configuration issue with your host, a caching issue, outdated or poorly-coded plugins or software, or broken code.
- HTTP 502 Bad Gateway Error or 503 Service Unavailable. While each of these errors are slightly different from each other, they both indicate a server-side problem. The most common cause for either of these errors is a sudden spike in traffic or http requests, but the same issues that could cause a 500 Internal Server Error could also cause a 502 or 503 error. If you aren’t expecting a huge surge in site traffic, there’s a good chance that you either have a faulty plugin or your site is under attack. Other potential causes of 502 and 503 errors are improper firewall configuration and content delivery network (CDN) configuration issues. If you’re using a shared hosting platform, another website on your server may be experiencing an issue that’s causing the entire server to go down.
- 401 Unauthorized, 403 Forbidden, and Connection Refused by Host. If you’re getting one of these error messages, it’s because you no longer have permission to access the content or server. 401 and 403 errors are usually due to file permissions or passwords being changed, while Connection Refused by Host could be an incorrect password or a server port configuration problem. If you haven’t changed your passwords or file permissions, then the culprit could very well be a hacker.
Don’t see your error listed here? Check this comprehensive list of errors that prevent your site from loading.
2. You can’t log into your WordPress dashboard.
If you can’t log into your WordPress dashboard, the first thing you should do is reset your password. If you manage a lot of websites, it’s possible that you simply forgot that you changed your password on a particular site.
If you aren’t receiving password reset emails, it could be because your site is using WordPress’ native PHP mail() function. Email providers like Gmail, Yahoo, and Outlook often block emails sent using the PHP mail() function. If you aren’t already using an SMTP server to send emails from your website, then this may be the culprit. If you haven’t experienced any issues with email deliverability in the past or if you’re already using an SMTP server for your site’s emails, then it may be time to worry about your account being compromised.
A hacker may have gained access to your account and changed your password and the associated email address. If you get an error that says, “Error: The username ‘yourusername’ is not registered on this site” it’s likely that the hacker deleted your account and created a new admin account for themselves.
3. You get a malware warning message when you search for your site on Google or when attempting to load your site.
Google Safe Browsing detects unsafe sites and displays a malware warning message when a user attempts to visit. All the major browsers use Google’s Safe Browsing data to alert visitors to the presence of malware. If you see this alert on your site, you have probably been hacked.
4. Changes appear on your site that you haven’t made.
Some hackers will inject content in an attempt to phish personal information from visitors or redirect them to other websites for nefarious purposes. If you see any content on your site that you or another authorized user did not create, it’s likely that it’s been hacked.
These changes could be something as obvious as your entire homepage being replaced with new content, a strange popup, or ad placements on a site that shouldn’t be serving ads. But it could also be something more inconspicuous, like links or buttons on your site that you didn’t create.
Sometimes hackers will use comment spam or hide links in places that make it difficult to track them all down. They may add links to out-of-the-way places like your footer or insert them randomly into article copy. Or, they might swap out links on buttons you already have on your site.
5. Ads on your site are directing users to suspicious websites.
If you do normally run ads on your site, it might take you a while to notice if one of them is directing to a malicious website. Hackers that engage in “malvertising” use ads to route visitors to phishing and malware sites. It’s easy for these types of hacks to go unnoticed, especially in display network ads where the website doesn’t necessarily have control of the exact ads that display.
If you find ads like this that you host on your site, you should immediately remove the offending ad and the user account for the advertiser. If the ad is being served through a display network, you may temporarily disable ads on your site and notify the display network so they can remove it from their system.
6. There’s a sudden drop in performance on your site — it loads very slowly or reports timeout errors.
Your site may be loading, but if it’s unusually slow or you’re seeing server timeouts, the cause is likely an overloaded server. This could be from a hacking attempt, a faulty plugin, or something else on your site that’s taxing your server’s resources.
7. Your site is redirecting somewhere else.
This is bad news. If you try to visit your site and are instead taken to a different website, you’ve definitely been hacked. A hacker would need to gain access to the files on your server or to your domain registrar account.
If they managed to gain access to your registrar account, they could add a 301 redirect to your DNS entries. If they gained access to your site by cracking a WordPress admin password or getting your FTP credentials, they could add redirect code to a variety of files on your site, including your index.php or wp-config.php files.
8. Customers contact you about unauthorized charges.
If you’re using WooCommerce or another eCommerce system and are receiving complaints about unauthorized charges, you may have a data breach on your hands. Someone might have hacked into your website or payment gateway.
WooCommerce doesn’t store credit card numbers or security codes on your website, but other details like customer names, addresses, and emails are saved in your database. This information could be used by hackers to steal customers’ identities or initiate charges on stolen credit cards.
9. You notice new, unfamiliar user accounts or FTP/SFTP credentials.
You may not regularly check your list of user accounts. But if you’re running a large site that allows people to register for an account, make it a point to regularly check the user list in your WordPress dashboard for spam accounts. If you notice admin, editor, or store manager accounts that you didn’t create, you might have been hacked.
Spam accounts are often created by bots. They may not always gain access to any core file, but they can still cause serious damage by leaving spam comments that negatively affect your reputation, bloat your database, and direct your users to harmful websites or malware.
You may also want to pay close attention to your File Transfer Protocol (FTP) accounts. If you hired a developer to build your site and the technical work that you do to maintain your site is fairly limited, you may have never even looked at your FTP credentials. If you don’t have a copy of this information, you’ll find it in your web hosting account. Ideally, you should be using Secure File Transfer Protocol (SFTP) instead of FTP.
FTP access to your website is completely unsecured, transferring sensitive data in plain text for any hacker to access easily. SFTP encrypts information so that your commands, credentials, and other data stay safe.
When you set up your hosting account, a single SFTP user is usually automatically created. If you find more than one SFTP user or an unfamiliar FTP account associated with your site, this is cause for concern. Remove unfamiliar accounts and change passwords on your known accounts immediately.
10. You’ve been notified of a problem by your security plugin.
If you use a security plugin, you’ll receive an email if any suspicious activity is detected on your site. If your security plugin includes downtime monitoring, you’ll also be notified if your site goes down for any reason. These alerts can help you quickly identify, diagnose, and respond to anything from plugin vulnerabilities and fatal errors to hacking attempts.
11. Your web host has alerted you to an issue on your site.
Hosting companies hate hackers, spam, and bogged down servers, too, so they keep an eye out for any major issues with their customers’ sites. If your server is overloaded or if your host receives a lot of abuse claims regarding your domain, then they should swiftly contact you about the issue. If you’re getting messages from your host about a problem with your site, you should investigate as soon as possible.
Why has my WordPress site been hacked?
If you’ve been hacked, you’re probably wondering why. It can feel personal — and sometimes it is. If you run a website that deals with sensitive subject matter, you may be targeted by hacktivists. Or maybe you have an employee that’s taking advantage of their access for personal gain or a disgruntled former hire who’s out for revenge.
But most hackers aren’t trying to accomplish some grand, complex agenda, and aren’t targeting you personally. They’re more often running simple schemes on easy targets to steal money, gather sensitive information, or cause trouble for the sake of causing trouble. If you left the front door of your house open all day, every day, you’d hardly be surprised if someone walked in and stole a few things. Your website isn’t any different. Poor security practices are the main reason any WordPress hacking incident occurs. Most WordPress hacking attempts target unprotected or outdated sites.
Despite the fact that many small businesses don’t think cybersecurity is a high priority, the truth is that 43% of cyber attacks are directed at small businesses.
Small businesses are less likely to have the knowledge and resources to keep their sites secure and protected. Even the biggest corporations who have teams dedicated to online security still manage to get hacked from time to time. But the millions of small businesses that leave their sites unprotected are the easiest to attack — and that’s why hackers target them.
Top five ways a WordPress site gets hacked
What are the most common ways that WordPress site owners leave themselves exposed to hackers? While there are a lot of different methods hackers can use to gain access to your site, here are the top five:
1. Outdated plugins, WordPress core, and theme files
Outdated software and site frameworks are one of the most popular ways for a hacker to gain entry to your site. Since WordPress powers 42% of all websites, it’s unsurprising that sites using WordPress are common targets for hackers. With 54,000 free plugins in the WordPress directory alone, there’s ample opportunity for hackers to exploit poorly-coded, abandoned, or outdated plugins.
Usually when new versions of plugins are released in order to fix a security vulnerability, that vulnerability will be made public. Not publicizing it until after the fix is released prevents hackers from taking maximum advantage of that information, but once it’s released, hackers will rush to exploit those backdoors for as long as they can.
At least 33% of all WordPress sites use outdated software, leaving them exposed to hackers who now have the information they need to get in.
2. Brute force attack vulnerabilities
Brute force attacks use software that tries different combinations of usernames and passwords until the correct combination is found. The following insecurities on your site can increase the chances of a brute force attack:
- Not limiting login attempts. If you don’t set a limit on login attempts, a hacker can try an infinite number of usernames and passwords. This can eventually lead to them getting access to your site (at worst) or putting a huge load on your server and shutting it down (at best).
- Short or easy to guess passwords. The shorter your password or the fewer types of characters that are used, the easier it is for a hacker to crack with a brute force attack. With so many people using passwords like ‘123456’ or ‘password,’ you can imagine why brute force attacks are so common.
- No CAPTCHAs on your login form. CAPTCHAs are used to verify that the person attempting to log in or submit a form is a human. Since most brute force attacks are performed by bots, CAPTCHAs are very effective at preventing these types of attacks.
- Not using two-factor authentication. Two-factor authentication (2FA) uses extra security measures beyond a password to authenticate a user. It might be a security question like, “What is the name of your first pet?,” a code sent to the user’s email address or phone number, or a third-party authenticator app. If you’re not adding this extra layer of security to your site, it makes it much easier for a hacker to break in.
- Not having brute force attack protection. A brute force attack protection tool blocks suspicious bots and people from accessing your site automatically.
3. Insecure hosting
If your site doesn’t have an SSL certificate or uses FTP instead of SFTP for server-level access to your site, your hosting is insecure. Secure hosting uses Secure Socket Layer (SSL) encryption to keep communication between your website and browsers secure. Shared hosting environments can also weaken your site’s security. If another website on your server experiences a breach, your site could be impacted as well.
4. File permissions
Your site’s files have permissions associated with them that grant varying levels of access. If your WordPress file permissions are set incorrectly, it could give hackers easy access to important files and sensitive data.
5. Password theft
Tens of millions of passwords are stolen every year. You may get data breach notifications from Google if you store passwords in your browser. Google will compare your stored passwords for certain websites against a list of known data breaches and send you an alert if it finds your information in a list of leaked passwords. Not changing compromised passwords once you’re made aware of them can easily lead to being hacked.
How do I fix and restore my hacked WordPress site?
Don’t panic! Take a deep breath and stay calm as you follow these steps to recover your site and protect yourself from future hacks.
Before we take a deep dive into this topic, there are a few simple things you can do in an attempt to troubleshoot issues that you’re seeing on your site before jumping to the conclusion that you’ve been hacked:
- Wait a few minutes and reload the page
- Clear your cache and cookies
- Flush your DNS cache
- Restart your browser
- Restart your device
If these quick steps don’t resolve your issue, it’s time to do more investigating.
1. Determine what happened
If you’re able to log into your site and have a WordPress security plugin to monitor activity (such as the Jetpack activity log), check to see who logged in, when, and what they changed.

This can help you figure out which files are affected, along with which user accounts need to be reset. Make a list of anything suspicious that you find.
If your security plugin doesn’t have an activity log, you don’t have a security plugin, or you can’t access your site at all, you should contact your web host and ask them to check your server’s error logs. Their tech support team might not be able to pinpoint exactly what’s going on, but they should be able to at least gauge whether the problem is coming from the server, your plugins, an incorrectly configured .htaccess or .wp-config file, or a site hack.
If it seems like the problem is most likely a software or server issue, you’ll want to learn more about troubleshooting issues with WordPress. If it seems like you’ve been hacked, then it’s time to clean and recover your site by moving to the next step.
2. Use a site scanner to detect malware and repair your site
There are several excellent site scanners that will search your website for malware, injected code, modified core files, or other red flags that indicate a hack. Be sure to cross reference your activity or error logs for any files you flagged.
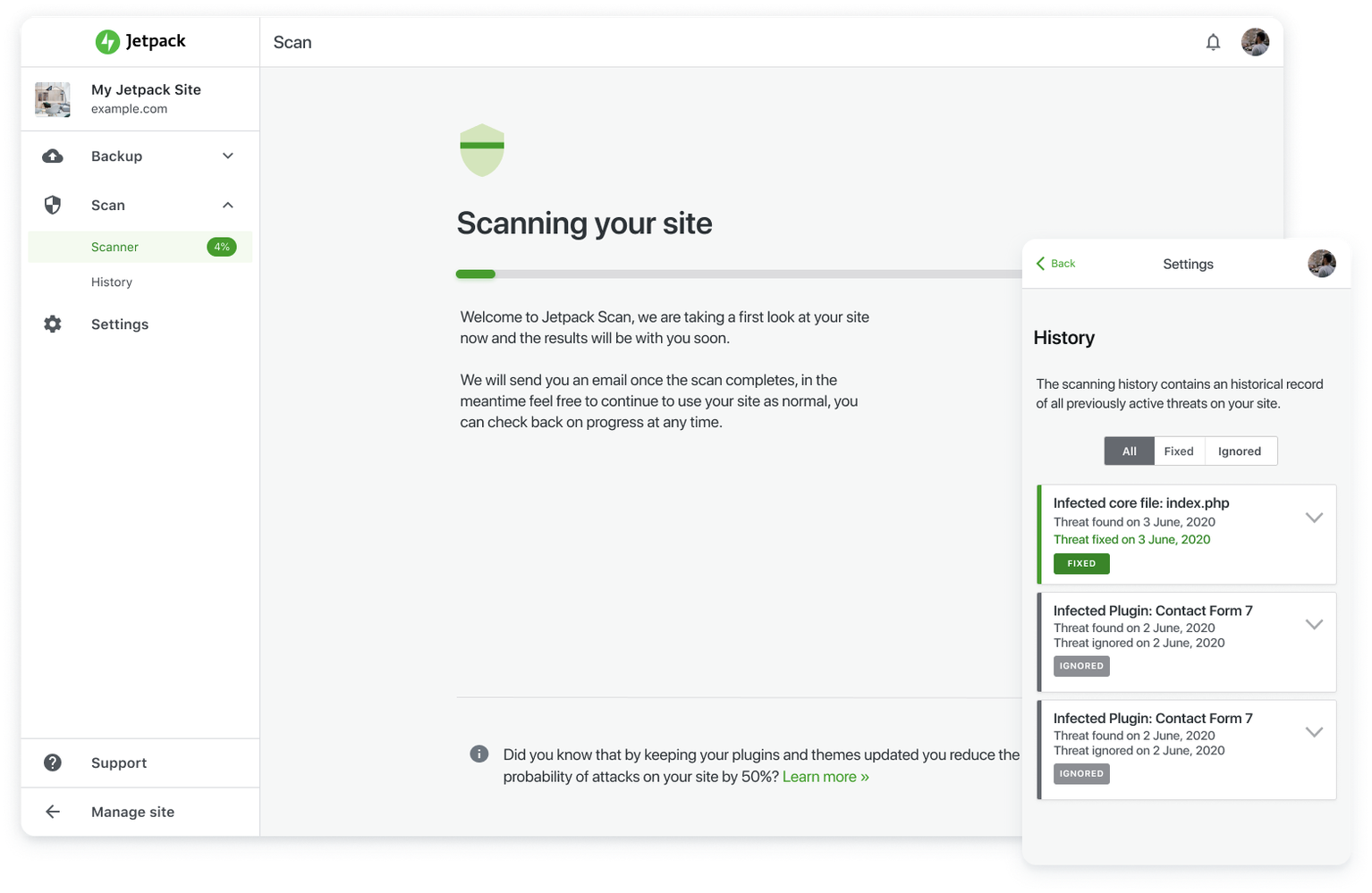
A good WordPress website scanner will also be able to repair any problems that it finds. One benefit of Jetpack Scan is that it has one-click fixes for the majority of known malware problems. And as an added bonus, it will protect your WordPress site with ongoing, regular malware scans.
If you don’t have a malware scanner and you can’t get access to your site to install a plugin for one, you can try using a free web-based scanner like PCrisk. It won’t be able to remove the malware, but it will at least help you identify if there is malware on your site so that you can attempt to remove it manually.
3. Restore from a backup, if possible
If you aren’t able to remove the malware or you aren’t sure that your website has been entirely disinfected, you might want to restore from a backup instead. Your host may keep backups of your site or you may be using a WordPress backup plugin like Jetpack Backup already. Jetpack stores multiple copies of your backup files on the same secure servers that WordPress uses for their own sites — not only are they protected from infection, they can also be restored if your website is completely down.
Restoring from backups isn’t foolproof though. While the most important part is recovering control and function of your website and removing all traces of the hacker, you may still lose some significant data. If you don’t know how long your site has been hacked, it’s possible that your backups may also be compromised.
If you run an eCommerce site and have customer orders stored in your database, reverting to a backup (unless you have real-time backups from Jetpack) could delete hundreds of customer orders that you haven’t yet processed. You may also lose customer reviews, blog posts, and any major changes you may have made to your site between the time of the hack and the backup you’re restoring from.
If you don’t have backups of your site or they’re all compromised, hope is not completely lost. Even if you need to rebuild your site from scratch, you can check the Wayback Machine for previous snapshots of your website. While it won’t restore the files, if you have to rebuild, you may be able to recover a lot of the content.
4. Reset all passwords and delete suspicious user accounts
Just removing the malware or rolling back to a previous version of your site will not be enough to keep things safe. No matter what, always reset ALL of your passwords and the passwords of other high-level users after your website has been hacked. Use the “suggested password” button on the WordPress profile page to make sure your new passwords are long, complex, and hard to guess. Concerned about remembering your combination? Try a password manager like LastPass or 1Password.
If your activity log shows any suspicious logins, then remove those accounts. If you find any extraneous or spammy-looking user accounts, no matter their level of access, you should probably delete them as well to be safe. Just because a hacker used one account for a malicious activity doesn’t mean they didn’t create multiple accounts so they could keep coming back.
5. Call in an expert
Some hacks are more complex, can’t be cleaned by an automatic site scanner, and are beyond the average user’s ability to identify and remove. These cases might involve intricate systems of injected code or access rules that can hide in multiple files.
If you feel like you’ve done everything you can and your site is still compromised, or you would just feel safer if someone knowledgeable double-checked things for you, you’ll want an expert to take a look. If you don’t know anyone with this type of expertise, consider hiring a WordPress recovery professional from Codeable.
6. Update your software
Since most WordPress hacks exploit vulnerabilities in outdated software, it’s important to get the latest versions of your plugins, theme, and WordPress core onto your site as soon as possible.
Before you start updating, take a full backup. When the backup successfully completes, start by updating WordPress core first, then your plugins, then your theme.
Note: if you are using WooCommerce, always update your WooCommerce extensions first, then update WooCommerce.
7. Resubmit your site to Google
If your site was blocklisted by Google, resubmit your clean website to restore your good name. You’ll know you’ve been blocklisted if a warning appears next to your site in search results or if you no longer appear for searches you once ranked for. Note, though, that there could also be other reasons that you no longer appear in search results.
To remove your site from this list, use Google Search Console to request a review.
How do I prevent my WordPress site from being hacked?
Preventing a hack is always a much better solution than trying to recover from one. Make sure your WordPress site is protected by implementing the following:
1. Use a security plugin.
Security plugins use a variety of measures to help protect your site from hackers. Some will also notify you of suspicious activity or downtime. Jetpack Security provides essential features like:
- Real-time backups
- Real-time scanning
- Spam prevention
- A web application firewall (WAF) to protect your site around the clock
- An activity log
- Downtime monitoring
- Brute force attack protection
Using a security plugin takes most of the hard work and technical expertise out of protecting your website so that you can spend more time focusing on creating content, making sales, or finally relaxing for a few minutes.
2. Keep WordPress, plugins, and your theme up to date
Updating your software after a hacking incident is a great way to help close those backdoors into your site, but doing it once isn’t enough. You’ll want to continue to keep everything up to date as much as possible going forward. You can do this by either monitoring and manually updating your software on a regular basis, taking advantage of Jetpack’s auto-update feature, or checking with your hosting provider to see if they offer automatic updates.

Even though keeping your software up to date will improve your site’s security, you should also be aware that updates can sometimes result in plugin or theme conflicts. You’ll still want to check your site’s functionality regularly to make sure everything is working correctly.
3. Strengthen your login and form security
Protecting your login form, contact form, and comment submission form is one of the simplest things you can do to protect against things like brute force attacks and comment spam. Here are a few ways you can keep your forms safe and secure:
- Limit login attempts. If you freeze out users for a period of time after several login attempts, this will prevent most brute force attacks entirely.
- Require stronger passwords. Require users to create longer passwords of at least 16 characters and a combination of lower and uppercase letters, numbers, and special characters. The longer and more complex the password, the harder it will be for a hacker to crack.
- Use a CAPTCHA on all forms. CAPTCHAs will help verify that the user is human. Not only do they do a great job of preventing bot attacks, they can help mitigate comment spam.
- Require 2FA for all users. At the very least, you should require two-factor authentication for your admin accounts or any account that may have access to sensitive information, like customers.
- Use an anti-spam plugin. Jetpack Anti-spam is built with Akismet, the most robust anti-spam solutions for WordPress. While comment spam isn’t quite the same risk level as someone gaining access to admin-level data, it can still be a big security and reputation risk. Eliminating or greatly reducing comment spam is as easy as a one-click install with Jetpack.
4. Switch hosting providers or environments.
Hosting is one place you should never skimp when it comes to your website. A high-quality hosting package will help protect your site with its own firewall, SSL certificate, system monitoring, and WordPress-optimized configuration.
If you’re on a shared hosting environment that was the cause of your woes, but you otherwise like your current host, you can ask about options for cloud, VPS, or dedicated server hosting.
5. Make your own automated backups
Even if your hosting package includes backups, there’s a lot to be gained by generating your own off-site backups. Most hosts will only make backups daily or weekly and store them for 30 days. And if they’re saved with your host, they could be compromised at the same time as your site.
If you use a separate WordPress backup plugin, like Jetpack Backup, your files are stored separately from your host, you have more granular control over what parts of your site are restored, backups are stored for up to one year, and you can take care of everything from anywhere with the Jetpack mobile app.
The all-in-one prevention and recovery tool
A good security plugin can prevent the majority of most common hacks and even help you recover if you’ve already been hit. Jetpack was designed to cover all of the most important bases and provide an intuitive and reliable way to recover in an emergency.
Jetpack’s support team of Happiness Engineers love nothing more than to help site owners overcome issues and beat cybercriminals at their own game. It’s this community-first, team approach that led Jetpack to become one of the most popular WordPress plugins of all time.
Secure your WordPress site with Jetpack Security.
FAQs about WordPress hacks
How often are WordPress sites hacked?
While there aren’t any concrete statistics on exactly how often WordPress sites are hacked, globally there are 30,000 websites across all platforms hacked every day. Since WordPress powers nearly 40% of all websites, it’s plausible that 10-12,000 WordPress sites are hacked each day.
What are the most common types of hacks?
- Bait and switch. This is used by hackers primarily on online ads or ad networks. They’ll pose as a reputable brand, but the ad link will take the visitor to a malicious site that attempts to phish information, get them to make fraudulent purchases, or download malware onto their devices.
- SQL injection. This technique involves the hacker uploading SQL commands to a site to steal or alter server data, usually for the purposes of identity theft, making illegal transactions with financial information, or just the fun of destroying someone’s entire database. These attacks are commonly made via insecure web forms, cookies, or other user input that hasn’t been validated.
- Credential stuffing. Generally performed by bots, credential stuffing uses a list of stolen usernames and passwords to automatically make login attempts on your site. The goal is to gain enough access to your site that they can initiate unauthorized transactions, steal personal information, redirect visitors to harmful websites, or use your site to bulk-send phishing emails. Learn more about this cyber security attack in our guide on what credential stuffing is and how to prevent it.
- Clickjacking. With clickjacking, a hacker will use code to create multiple content layers with the intent of getting the user to click something unintentionally. They may think they’re clicking on your About page link, but really they’re clicking on an obscured link that takes them to a malicious site. Hackers can also use this technique to steal passwords by creating “invisible” forms on top of legitimate ones. Users will think they’re logging into one of their own accounts when, in reality, they’re sending this information straight to a hacker.
- Cross-site scripting (XSS). This is similar to SQL injection in that it uses the same entry points — insecure forms and other unvalidated user input — but the code that is injected is Javascript or HTML and sometimes VBScript or Flash.
- Man-in-the-middle attacks. These attacks usually happen in public spaces because hackers use insecure routers to intercept data as it’s being transmitted. They can use this technique to acquire usernames, passwords, financial records, and other personal information to target your websites and any other account they’ve managed to get information for.
- DDoS and brute force attacks. Distributed Network Attacks (DDoS) involve sending a high volume of requests to a website in an attempt to crash the server. Brute force attacks are a type of DDoS attack that tries different combinations of usernames and passwords in your site’s login form in an attempt to gain access. This will create a high volume of requests and, if not caught and stopped, can cause your server to overload and stop responding.
- DNS hijacking. This method is often used with the intent to redirect your website to a different website (DNS spoofing). With DNS hijacking, a hacker gains access to your registrar or your active nameserver and points your IP address or uses redirects to send visitors to harmful sites.
What are the consequences of my WordPress site being hacked?
If there’s nothing of much importance on your site or the hack isn’t really affecting performance in any way, why should you worry about your site being hacked?
Even if the hack isn’t directly affecting you and your site, it’s going to affect other people. You might not notice, but a hacker might be phishing personal information from your visitors so they can steal their identities, redirecting them to sites that download malware onto their devices, or using your servers to send spam or dangerous content to people all over the world.
It might not affect you immediately, but it may cause your site to get blocklisted or your hosting provider to remove your site from the server. If the hacker does end up causing harm to a user of your site, you could be held liable if the claimant files a negligence claim against you.
How do I turn a hacker in to the authorities?
Most hacking crimes are difficult to prosecute. The hacker may be in another country, or the value of the damage is too low for authorities to prioritize. If you’re in the US, the FBI recommends reporting the crime to them. The more complaints that are filed, the better chances they’ll have of being able to build a case. If you know who the hacker is — like an employee or personal acquaintance — it may be easier for the FBI to respond.
We guard your site. You run your business.
Jetpack Security provides easy‑to‑use, comprehensive WordPress site security, including real‑time backups, a web application firewall, malware scanning, and spam protection.
Secure your site