WordPress is one of the safest content management systems (CMS) you can use to run a website. Still, every software comes with vulnerabilities and security issues, most of which are dependent on user behavior. If you don’t know what these issues are or how to prevent them, even the most secure software might not be able to safeguard your website from attacks.
The good news is that protecting WordPress sites is easier than with other systems because you have access to powerful security plugins. Combine that with safe credentials and all but the most sophisticated attacks won’t stand a chance of breaching your site.
In this guide, we’ll talk about the importance of prevention when it comes to keeping WordPress secure. Then, we’ll discuss the most common types of issues WordPress site owners may encounter and what types of attacks websites fall prey to most often.
From your first initial WordPress installation to managing a bustling, successful site, we’ve got you covered.

The importance of closing all potential security vulnerabilities
The concept of keeping your website “safe” can be a bit nebulous. When people talk about protecting your site, they’re usually referring to keeping unauthorized WordPress users from making changes to it, preventing malicious files from getting uploaded, or reducing the chances of data breaches.
Failing to protect your website from potential security breaches can affect you in a multitude of ways, even if you’re not dealing with a large amount of sensitive user information. For instance, if you run a small but established online business, security issues can negatively impact the way customers perceive you.
To understand how important it is to prevent security issues, let’s elaborate on why they can be so damaging:
- Unauthorized access. Many updates for WordPress sites contain patches for security vulnerabilities that have been discovered since the previous version was released. If your website isn’t updated, it’s at risk of being accessed and exploited by hackers who are aware of these vulnerabilities.
- Loss of confidential information. If your website gets compromised, malicious actors can gain control of your site and sensitive data, including user information and other confidential materials. If you’re running an online store or any other type of site that handles private user data, this could have serious implications, both legally and in terms of your reputation.
- Poor website performance. If someone gains access to your website, they can modify how it works and negatively impact its performance. In some cases, attackers might not even need to gain entry to bring a website “down”, like with Direct Denial of Service (DDoS) attacks.
- Breach of compliance. In certain industries, failing to secure user data can put you in breach of regulatory compliance. For example, in the healthcare and financial sectors, companies are required to use up-to-date software to ensure the highest level of data security. And sites that accept credit card payments must comply with the Payment Card Industry Data Security Standard (PCI DSS).

If you run a WordPress website, security is of the utmost importance. Shoring up your website from the very beginning will prevent the most common types of issues and help you keep user data safe.
How to uncover security vulnerabilities on your WordPress site
Unfortunately, it’s possible to use an infected computer without knowing it. In a lot of cases, devices end up riddled with malware and users are none the wiser.
The same can happen with a website. Your WordPress site might be vulnerable to attacks, or it could already be infected with malware. Unless the attackers make it obvious, or you have access to the right tools, this can be hard to spot.
Just as you have antivirus software for computers, there are also security scanners for WordPress. Tools like Jetpack Security can scan your website for WordPress security vulnerabilities and let you know if there are any issues or irregularities you need to fix.
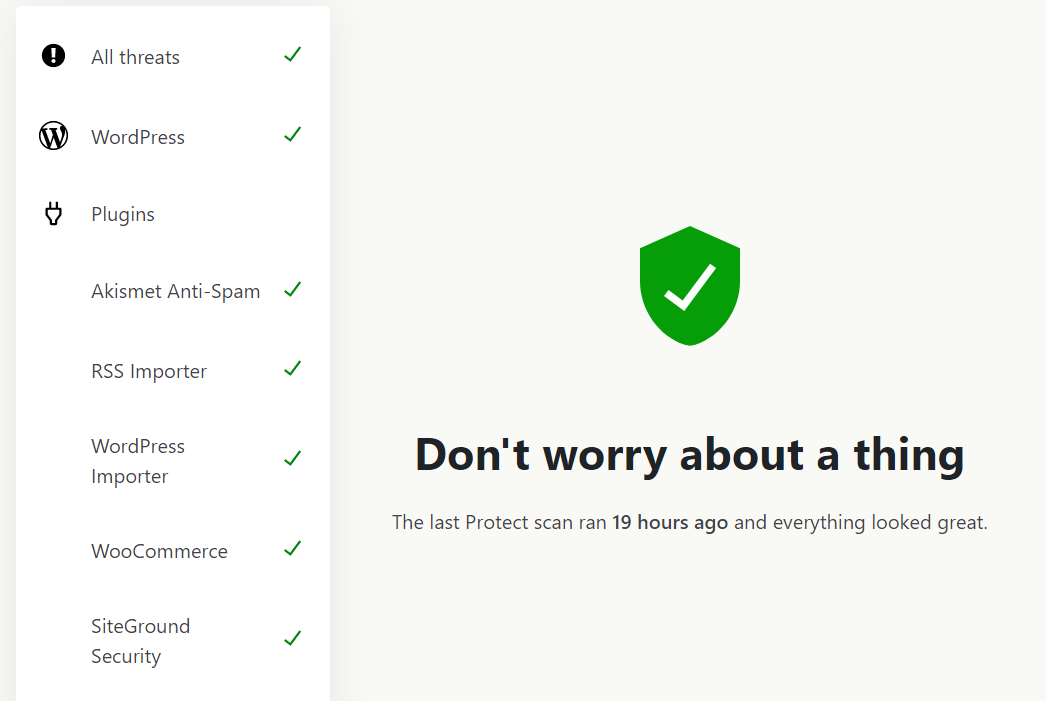
Jetpack Security’s Scan tool relies on the WPScan vulnerability database, which is used by enterprise companies. That means the database is very comprehensive, and has the ability to identify the most common vulnerabilities your site may face.
Plus, Jetpack Security is an easy-to-use security plugin developed by Automattic, the company behind WordPress.com. In addition to Jetpack Scan, it includes VaultPress Backup and Akismet. So, when you opt for this tool, you’ll be able to protect your site from vulnerabilities as well as spam, and you’ll get advanced backup features, too.
The 20 most common WordPress security issues and vulnerabilities
In this section, we’ll focus on the most common security issues seen in WordPress sites. Every single one of these issues can lead to vulnerabilities that attackers can exploit.
This can be a lot of information to digest, so don’t be overwhelmed. We’ll tell you what you need to know about each security issue, and provide some additional resources to learn more about them and how to fix them.
1. Lack of WordPress security plugins
Security plugins are among the most popular WordPress tools. Depending on which plugin you use, it may be able to scan your website for malware, set up a firewall, help you create backups, prevent spam, and more.
You can do everything that a security plugin does manually. But, that typically involves customizing many aspects of your site on the back end. For instance, editing core files to block suspicious IPs. As you can imagine, manually securing your site can be very time-consuming.
The beauty of security plugins is that they can save you a ton of time and hassle. What’s more, they can act as all-in-one solutions for a lot of the more common WordPress vulnerabilities.
WordPress plugins offer different functionality, so we recommend opting for a tool that covers as many vulnerabilities as possible, like Jetpack Security.
As we mentioned, Jetpack Security can help you automate backups, keep security logs for your site, set up a firewall, scan your site for malware, and more. Plus, it integrates with Akismet to help you prevent spam in comments and forms on your site.
2. Lack of regular site scans
Regular site scans are like health check-ups and should be on every WordPress security checklist. They help you identify threats like malware infections, security loopholes, and unusual activity.
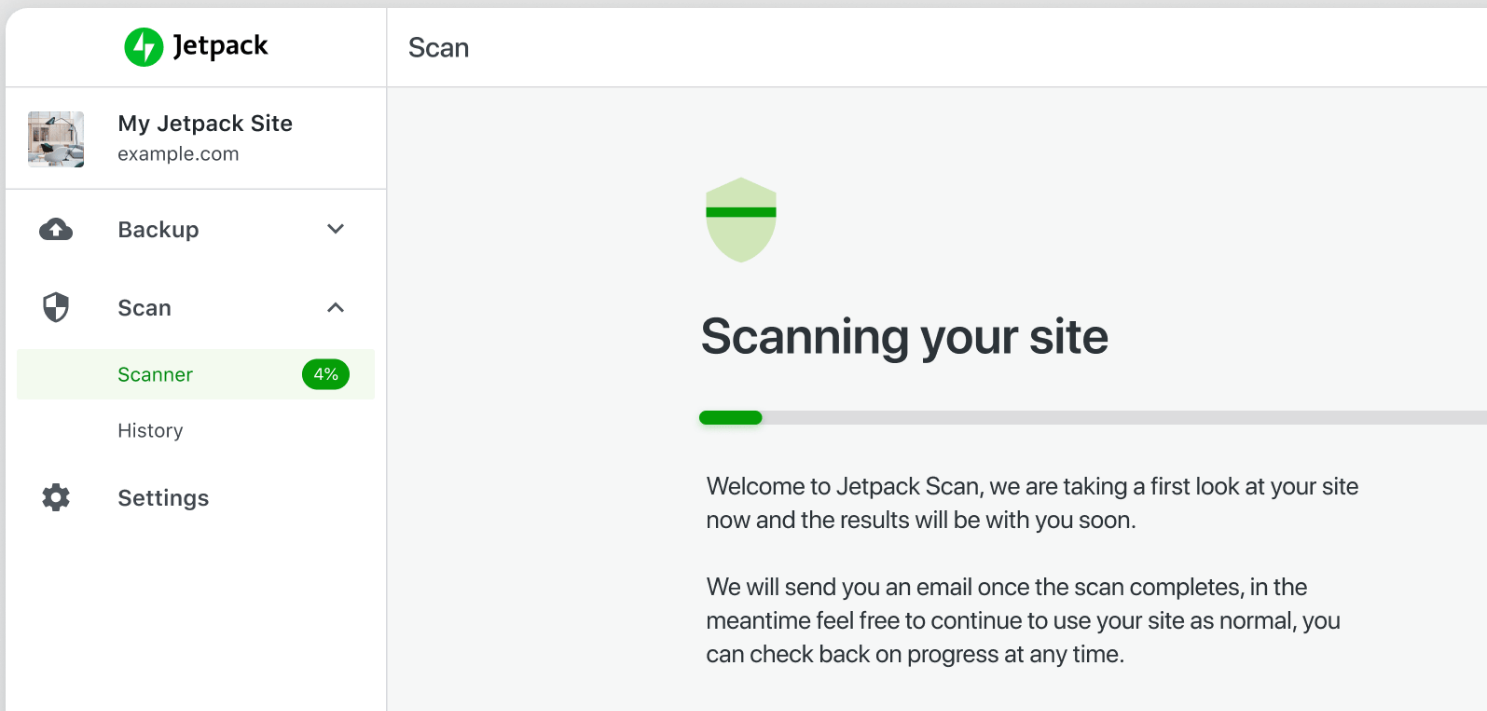
To put it simply, if you’re not running regular scans on your WordPress website, you’re leaving it vulnerable to security threats. This can lead to a compromised site, loss of sensitive data, damaged search engine rankings, and a loss of trust from visitors.
Site scan tools typically run in the background without affecting any functionality. So, if you have a security plugin or scanning tool, it’ll usually run automatically every so often and only alert you if it finds anything wrong with your website.
Think about site scanners like antivirus tools for your website. Every modern operating system (OS) comes with built-in malware scanners and removal tools, even if you’re not aware, they’re running in the background. These tools help keep your computer safe and, without them, your experience would be a lot worse.
3. Lack of regular site backups
Backups act as a safety net, preserving your site’s data in case of technical mishaps or security breaches. Without regular backups, you could lose all website content and user data.
Perhaps the biggest advantage of regular site backups is that they provide you with restore points in case you run into any issues. Instead of spending hours or days troubleshooting security breaches, you can simply revert your site to a previous state without losing critical data.
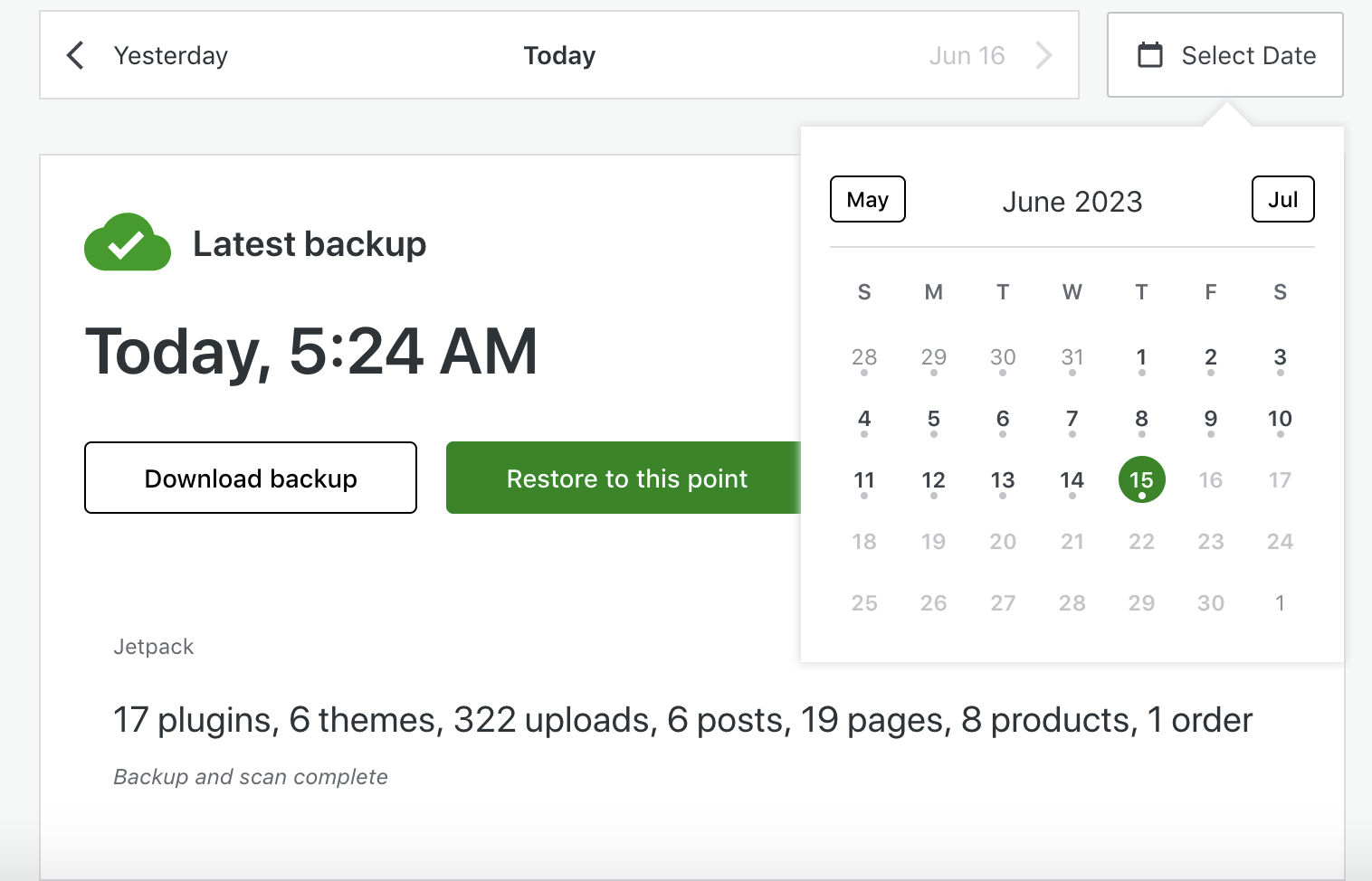
Ideally, backups should be automatic, and you shouldn’t let too much time go between them. Plugins like Jetpack Security include backup tools that enable you to save your website’s information to the cloud. With VaultPress Backup (which is part of Jetpack Security), you’ll get access to real-time backups any time you make changes to your website.
4. Outdated WordPress versions or plugins
Keeping your WordPress core and plugins updated is crucial for your site’s security and functionality. That’s because outdated software versions tend to have known vulnerabilities that hackers can exploit.
On top of that, they may cause compatibility issues affecting your website’s performance. This could lead to compromised data, loss of site functionality, and a poor user experience.
If your WordPress website has a bunch of pending updates, then it’s time to get to work on updating all of its components. You can also enable automatic updates for WordPress core directly from the Dashboard → Updates screen.

5. Outdated PHP version
Hypertext Preprocessor, or PHP, is the backbone of WordPress. It’s one of the main programming languages that the CMS is built on. Using an outdated version of PHP can lead to WordPress security issues and compatibility issues.
Newer versions of PHP also improve performance drastically. Typically, your web host will update your server to use newer versions of PHP as they come out. If you want to double-check what PHP version you’re using, you can do so directly from WordPress.
6. A hosting environment that’s not secure
Your hosting provider’s job is to help you build a website by providing you with the best resources possible. That means a stable server with decent hardware, an easy-to-use hosting management dashboard, and solid security measures.
If your web host doesn’t provide you with basic security settings, it’ll impact the way you run your website. Basically, you’ll have to spend a lot more time working on covering basic WordPress security vulnerabilities instead of working on your site.
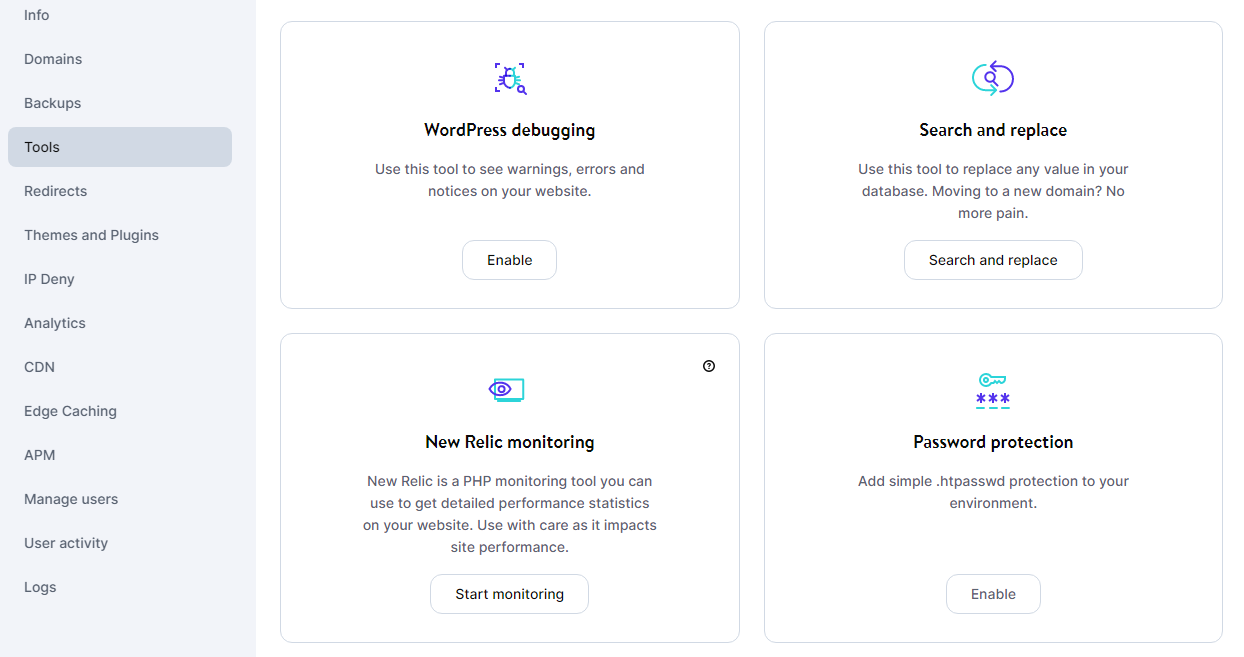
A secure WordPress hosting provider will offer features like automated backups, Web Application Firewalls (WAFs), automatic blocking on known-malicious IPs, DDoS mitigation, and more. If you’re using a web host that doesn’t offer decent WordPress security measures, we recommend switching to a higher-quality WordPress hosting provider.
7. Weak password and login credentials
Using weak passwords and login credentials is probably the most common security issue with WordPress websites. In fact, this is a massive problem for any site or software that requires you to log in.
It’s important to note that this doesn’t just include the WordPress admin login page. Weak web hosting and File Transfer Protocol (FTP) credentials can also lead to vulnerabilities.
Simply put, most users don’t like the hassle of complicated, unique passwords for every application they work with.
Although weak and recycled passwords may be easier to remember, they can put your site at risk. That’s because they make it much easier for attackers to brute force their way into websites or use leaked credentials to gain access to accounts on other platforms.
If you want to keep your site safe, anyone with access to critical tools will need to learn how to use secure credentials, only creating strong passwords and usernames. Additionally, adding support for Two-Factor Authentication (2FA) can help you further secure your site.
8. Lack of 2FA
Two-Factor Authentication, or 2FA, adds an extra layer of security by requiring a second verification step during the login process. This makes unauthorized logins significantly harder, since attackers would also need access to your email account or phone, depending on which type of 2FA you configure for your site.
There’s no reason not to offer 2FA as an option on your website. Implementing the system is remarkably easy and there are a lot of WordPress plugins, including Jetpack, that can set up 2FA for you.
9. Insecure login data storage
Storing login data insecurely, like in plaintext (or using a Post-it), is akin to leaving your bank details out in the open. Poor storage practices make it easy for attackers to obtain these details if they gain access to the location. This can lead to unauthorized access, data breaches, and potential loss of website control.
As a rule of thumb, don’t store login information anywhere where other people might get access to it, be it physically or digitally. If you have to store login credentials, use a password storage tool, like 1Password, that can encrypt that data for you.

10. Mismanaged and undefined user roles
Poorly managed user roles can lead to users having more permissions than they need, which creates security risks. This can result in unauthorized or accidental changes to the site, data leaks, or a misuse of resources.
Ideally, the Administrator should be the only person with full access to the WordPress backend. For every other user role, accounts should be granted the bare minimum permissions needed to perform their duties.
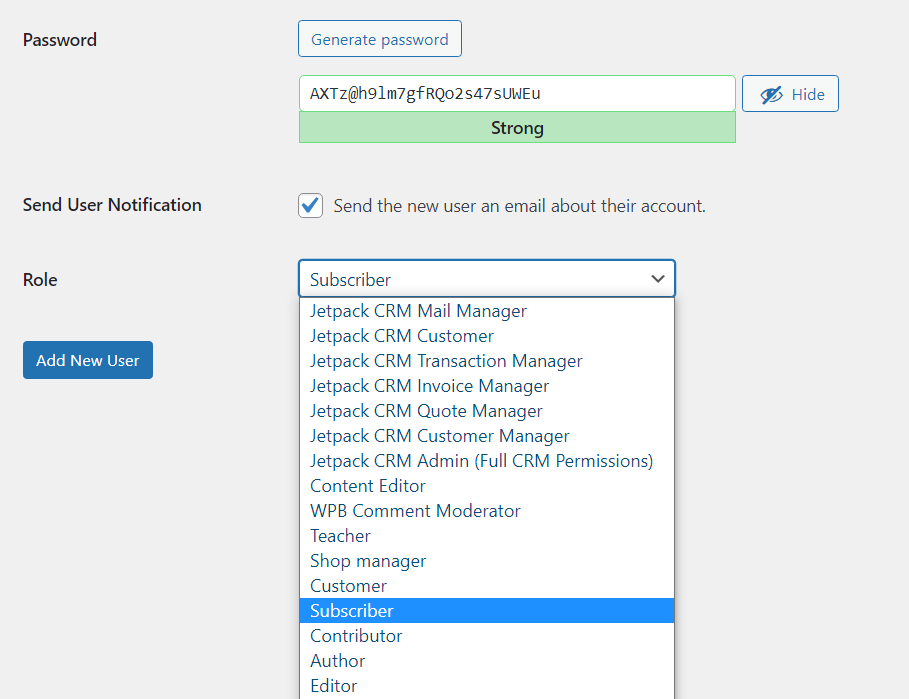
The good news is that WordPress gives the Administrator full control over user role assignments. Plus, each role comes with a defined set of permissions to match their duties. And, if you want to create additional roles or modify their permissions, you can do so using WordPress plugins.
11. Insufficient monitoring of user logins and activities
Without adequate monitoring, you may miss suspicious behavior or malicious activities on your site. This lack of visibility can lead to unauthorized changes, data breaches, and system misuse — all of which can harm your site’s functionality.
Out of the box, WordPress core doesn’t offer any security log functionality. But, you can use plugins like Jetpack with its activity log feature to keep track of what’s happening on your website (and who’s accessing it).
Some WordPress web hosts also give you access to activity logs at the server level, which enables you to monitor if anyone makes changes to its configuration.
When using this type of tool, it’s best to configure notifications for specific types of activities, like failed login attempts. That way, you’ll get a heads-up if anything sketchy is going on without having to read through dozens of pages of logs.

12. Themes and plugins containing vulnerabilities
WordPress themes and plugins with security vulnerabilities are often targeted by hackers. If they manage to exploit these vulnerabilities, it can lead to unauthorized access, data breaches, and more.
The good news is that this typically only happens if you use outdated plugins and themes. Likewise, it may be more likely to occur when you download “free” versions of premium plugins and themes from disreputable websites.
These free versions can include code that enables attackers to gain access to your site. So, unless you’re regularly scanning for vulnerabilities, it’s best to avoid this.
Still, there are plenty of quality plugins and themes that are also free. So, if you need to install one, it’s best to read through user comments on sites like WordPress.org before downloading them. A lot of users will share their stories of problems or WordPress security issues, which can help you make an informed decision.
The WPScan Vulnerability Database, maintained by Automattic’s security team and used by enterprise organizations, currently tracks thousands of known WordPress plugin vulnerabilities with detailed CVE classifications.
13. Misconfigured WordPress database
A misconfigured database can leave your site’s data exposed, making it susceptible to SQL injection attacks and/or data breaches. SQL injection remains one of the OWASP Top 10 Web Application Security Risks, and WordPress database misconfigurations create exploitable entry points.
One of the most common types of misconfigurations is using the default prefix for databases in WordPress (wp).
This makes it easy for attackers to identify the database and try to access it. Likewise, using weak credentials at the database level can leave it vulnerable.
Keep in mind that WordPress stores all your site’s content in a unique database. That means if someone gains access to the database, they can see everything on your website and modify critical settings.
14. A misconfigured content delivery network (CDN)
If your audience is spread around the world, implementing a Content Delivery Network (CDN) can be a great way to improve its performance for visitors who are further away from your servers. But, a poorly configured CDN may lead to security gaps.
Attackers could exploit these vulnerabilities to launch DDoS attacks, manipulate content, or gain unauthorized access to sensitive data. By misconfiguration, we mean human error in terms of what content the CDN caches, problems with the SSL/TLS configurations, or exposing the site’s original IP address.
Configuring a CDN can be tricky with some providers. If you’re looking for a straightforward option, Jetpack’s CDN is super easy to set up and use. There’s no configuration required, so you don’t have to worry about user error!

15. Insecure file and directory permissions
File and directory permissions determine who can read, write, and execute files on your WordPress website. These permissions are crucial for maintaining the security and integrity of your site.
If they’re insecure or misconfigured, they can leave your site vulnerable to various threats like attackers being able to upload malware or getting unauthorized access to files.
Unsecure files also open you up to potential data breaches. If the permissions aren’t set correctly, attackers will be able to read or modify the contents of files, which means they can steal or erase critical data.
16. Unrestricted public-facing file uploads
A lot of WordPress websites enable users to upload files through forms. This can be useful if you want people to be able to submit files for you to review, attach images to comments, and more.

Any form that enables users to upload and submit files to your site needs to be tightly secured. That means full control over what type of files people can upload, so they can’t use the forms to get malware on your server.
If you use a WordPress security plugin that offers real-time malware scanning, it should detect any malicious files that make it past your form’s security. Without security scanning, you may end up hosting malicious files that can give attackers access to your site.
17. Insecure third-party services and integrations
As you may already know, it’s common practice to use third-party services and integrations in WordPress. This can help you add new functionality. But, if you connect your website with a service that isn’t secure, you may end up with additional vulnerabilities on your website.
For example, if a third-party service provides an unsecure API for integration, it can serve as a gateway for attacks. Hackers can exploit weak API security to perform actions like injecting malicious code, stealing data, or disrupting your site’s functionality.
Third-party services with low-security standards can also compromise your credentials, which can give attackers access to your website if you’re not using 2FA or additional protections. In a nutshell, you should never connect your website with any third-party service unless you’re sure it’s reputable.
18. Unauthenticated AJAX actions
AJAX (Asynchronous JavaScript and XML) is a technique used to create dynamic, responsive web applications by sending and retrieving data from a server asynchronously. That means the sending and retrieval process doesn’t interfere with the page loading.
As far as WordPress goes, it’s common to use AJAX to handle data submission and retrieval in the background. For example, a lot of plugins use AJAX to power “infinite” loading of content. It’s also frequently used to enable instant search functionality on ecommerce sites.
Every AJAX action needs to follow security and authentication guidelines to keep your site safe. Without proper user verification, attackers can “trick” your website into performing actions that retrieve sensitive information from the database.

19. Misconfigured web servers
A web server that isn’t properly configured can be vulnerable from a security standpoint. By “server configuration”, we mean implementing basic security and access rules to protect it from attackers.
To give you an example, a secure server won’t allow visitors to execute code because they don’t have the right permissions. Likewise, a good security configuration will prevent known malicious IPs from interacting with the server using tools like a Web Application Firewall (WAF).
Unless you have direct access to the server, this security depends on your web host. Some web hosts take WordPress security issues more seriously than others, so it’s essential that you choose the right provider for your website.
20. Zero-day exploits and unknown vulnerabilities
There will always be new WordPress exploits and vulnerabilities that attackers will seek to use to damage your website.
Zero-day exploits and unknown vulnerabilities refer to security holes in software that are not known to the developers until they are exploited by attackers. The good news is that once attackers start targeting new vulnerabilities, developers usually patch them pretty quickly.
In theory, it’s impossible to prevent zero-day exploits because we don’t know what they are. Still, you can drastically mitigate the risk they pose by using a robust WordPress security plugin like Jetpack Security. Since Jetpack Scan (powered by WPScan) uses a comprehensive database that’s updated regularly, it will be able to quickly catch the newest WordPress security issues as they emerge.
The main types of security threats WordPress sites face
So far, we’ve focused on specific security vulnerabilities in WordPress and how they can affect your website. But, it’s important to understand what an “attack” or “breach” on your website can look like in real life.
Unlike in the movies, attackers usually aren’t typing away at a screen with neon letters to hack your website. In reality, “hacking” is a lot more interesting and attacks can come in many forms. So, let’s take a look at some of the most common WordPress security issues.
1. Malware and virus infections
You’re probably familiar with the terms malware and viruses. In the context of a website, malware (short for malicious software) and viruses are types of malicious code that can harm your site or its visitors.
Malware is typically inserted into your website, and can cause a wide range of issues. For instance, it can be used to deface your site, steal data, or even spread malware to its visitors.
Types of website malware can include backdoors (allowing unauthorized access), drive-by downloads (automatically downloading harmful software to a user’s device), and defacement (changing the visual appearance of your website).

2. SQL injection attacks
An SQL Injection is a type of attack that enables someone to interfere with the queries that an application makes to its database. In this case, the queries that WordPress submits to the database. The aim of this type of attack is to gain unauthorized access to information or to the site itself.
Here’s how it works: When WordPress takes user input, it structures it in Structured Query Language (SQL) to fetch the corresponding information from the database. If the query isn’t “sanitized” first, an attacker can modify it. These statements can manipulate the original intent of the query, leading to unauthorized data exposure, data modification, or even data deletion.
3. Cross-Site Scripting (XSS) attacks
Cross-Site Scripting, or XSS attacks, occur when an attacker manages to inject malicious scripts into web pages viewed by other users. These scripts are usually written in JavaScript and execute in the user’s browser.
Once an XSS attack is successful, the attacker can steal sensitive data (like session cookies) and impersonate the user. Depending on how much access the user has to the site, they can wreak a lot of havoc.
4. Cross-Site Request Forgery (CSRF) attacks
Cross-Site Request Forgery (CSRF), also known as XSRF, is a type of attack that tricks the victim into submitting a malicious request. It exploits the trust that a site has in a user’s browser, essentially using the identity and privileges of the victim to “infiltrate” it.
Suppose a user is logged into a web application where they can perform certain actions, like changing their email address. A CSRF attack could involve the attacker sending the user an email with a link or embedding a link on another website.
If the user clicks the link, it triggers a request to the web application that utilizes the user’s already authenticated session to perform the action — in this case, changing their email address to one controlled by the attacker.
5. Brute force attacks
A brute force attack involves trying multiple credential combinations until the right one is found. Attackers typically use bots or software to do this. Meaning, if your website doesn’t lock them out of the login screen, they may be able to try thousands of combinations.
These attempts can be random, but more often, attackers use a dictionary of commonly used passwords or employ more advanced methods like using lists of breached credentials from other sites.
6. DDoS attacks
Distributed Denial of Service (DDoS) attacks involve multiple computers connecting to a website at the same time to try and overload it. This is possible because every server can only handle so much traffic before it starts to drop requests or goes down temporarily.
Typically, attackers use a network of compromised computers to carry out DDoS attacks. Depending on how protected your site is, this type of attack can result in prolonged downtime.
7. Malicious redirects
A “redirect” is when you visit a URL and your browser sends you to a different address. This happens because the server you’re trying to access has instructions to redirect all or some traffic to that location.
There are a lot of reasons to use redirects. For instance, if you change domain names or want to avoid users visiting pages that no longer exist. But, if attackers have access to the server, they can set up malicious redirects sending users to dangerous websites instead.
8. File inclusion attacks
A file inclusion attack happens when an attacker manages to trick your website into including files from a remote server that they control. This type of attack typically exploits poorly validated or unsanitized user inputs.
Properly sanitizing inputs can help you prevent file inclusion attacks as well as SQL injections and other types of vulnerabilities. Another way to prevent this is by using a WAF and keeping your site updated to avoid holes in its security.

9. Directory traversal attacks
Directory or path traversal attacks involve attackers manipulating a URL in such a way that the server executes or reveals the contents of files located anywhere within its file system.
The goal of this type of attack is to gain access to files you don’t have permission to see or modify. The best way to prevent this type of attack is by configuring secure file and directory permissions.
10. Remote code execution attacks
A remote code execution attack happens when someone can execute harmful code remotely. For websites, this means attackers being able to execute malicious scripts on your hosting server.
This type of attack can happen if your server is vulnerable. Depending on the type of access attackers get, they could potentially run any command they want on the server.
11. Session hijacking and fixation attacks
A “session hijacking” is a type of attack that exploits the mechanisms that sites use to help you remain logged in across multiple visits. Typically, websites use cookies to store information about each session. If an attacker can “steal” these cookies, they can hijack the session.
In practical terms, this means the website will enable the attacker to use your account without having to go through the login process. Depending on what permissions the account has, someone can do a lot of damage with a hijacked session.
12. SEO spam
In terms of search engine optimization (SEO), spam can refer to reusing keywords, sharing the same links multiple times, and otherwise trying to game the algorithms that determine site rankings in results pages.
A lot of times, attackers will try to gain access to websites and use them to improve their own rankings. They can do this by using your site to excessively link to their own.
Depending on how aggressive the spam is, it can affect your own search engine rankings and lead to penalization. It can also erode the trust of your users because they might think you’re the one spamming them.
13. Phishing attacks
You’re probably familiar with phishing attacks. They involve pretending to be someone from an organization or a website to try and obtain login credentials or other critical information from a specific user.
For a WordPress website, this could look like a fake email asking users to reset their credentials and directing them to a page that saves their inputs. A lot of non-tech-savvy users fall for phishing attacks, so it’s important you try and educate your visitors about official communications from your site.
Frequently asked questions
If you have any questions left about WordPress vulnerabilities or the types of attacks you might run into, this section will hopefully answer them.

Is WordPress secure?
The short answer is yes. By design, WordPress is a secure CMS. What’s more, its core software is regularly updated for maintenance and security purposes.
But, just as with any other software, its security depends on how you use it.
If you don’t update WordPress and its components regularly and use weak login credentials, you’re exposing your site to a lot of risks.
What are signs a WordPress site has been hacked?
Sometimes, it can be hard to spot if a WordPress website is compromised. Still, there are a lot of telltale signs of attacks that can tip you off. For one, you may notice changes in key pages or differences in links.
If the site is hacked, some search engines will also outright warn visitors when they try to access it. Running into one of these security notices is a solid indicator that you should scan your website for malware and look into ways to remove it.
How can you remove malware from a WordPress site?
The easiest way to remove malware from WordPress is by having access to backups. If you use a malware scanner like Jetpack Scan, it can detect changes to your server files as well as harmful code.
You can purchase this tool on its own or get it as part of the Jetpack Security bundle.
This scanner may be able to clean your website by removing the malware or restoring a backup from when the server wasn’t infected.
How can you prevent brute force attacks on WordPress?
You can prevent brute force attacks on your website by using a firewall to block connections from known malicious IPs. Plugins like Jetpack enable you to do this and help protect your login page from repeated attempts to breach it.
What is Jetpack Security?
Jetpack Security is a service that includes VaultPress Backup, Jetpack Scan, and Akismet in one package. That means it helps you automate backups, set up regular malware scans, and protect your website from spam, all in one plan.
What is the WPScan vulnerability database?
WPScan is a database of WordPress vulnerabilities maintained by experts in the CMS and security professions. The database gets constant updates, and you can access it via WP-CLI if you’re a developer. Jetpack Protect uses the WPScan database to identify any potential WordPress security vulnerabilities or malware on your website.
We guard your site. You run your business.
Jetpack Security provides easy‑to‑use, comprehensive WordPress site security, including real‑time backups, a web application firewall, malware scanning, and spam protection.
Secure your site